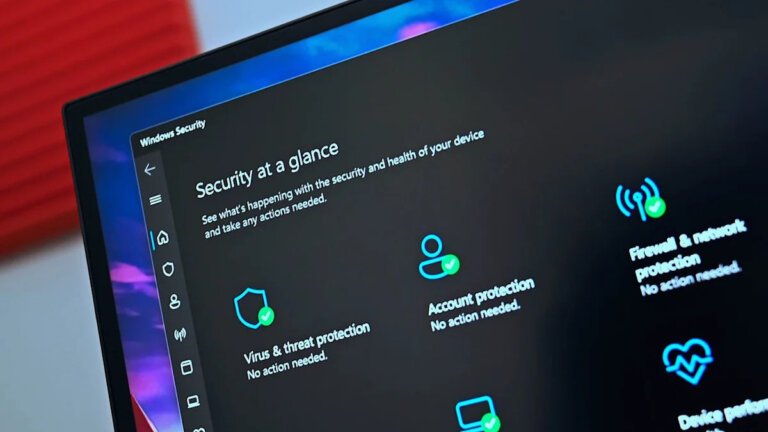
Microsoft stated that for many Windows 11 users, Microsoft Defender Antivirus offers sufficient protection without the need for additional software. Some users agree, believing that third-party antivirus solutions are becoming less necessary. However, others argue that the choice to use third-party software depends on individual usage patterns and feature needs. Microsoft acknowledged this, suggesting that users managing multiple devices or seeking extra services might still benefit from third-party options. An article promoting Microsoft Defender's adequacy was removed from the Learning Center, leading to a more balanced message that recognizes Defender as a strong baseline while acknowledging that third-party tools can provide additional capabilities. Microsoft promotes Defender as typically sufficient when Windows 11 is properly configured, offering features like automatic threat scanning and cloud-based intelligence updates, but also notes that some third-party tools offer features such as identity monitoring and built-in VPNs.