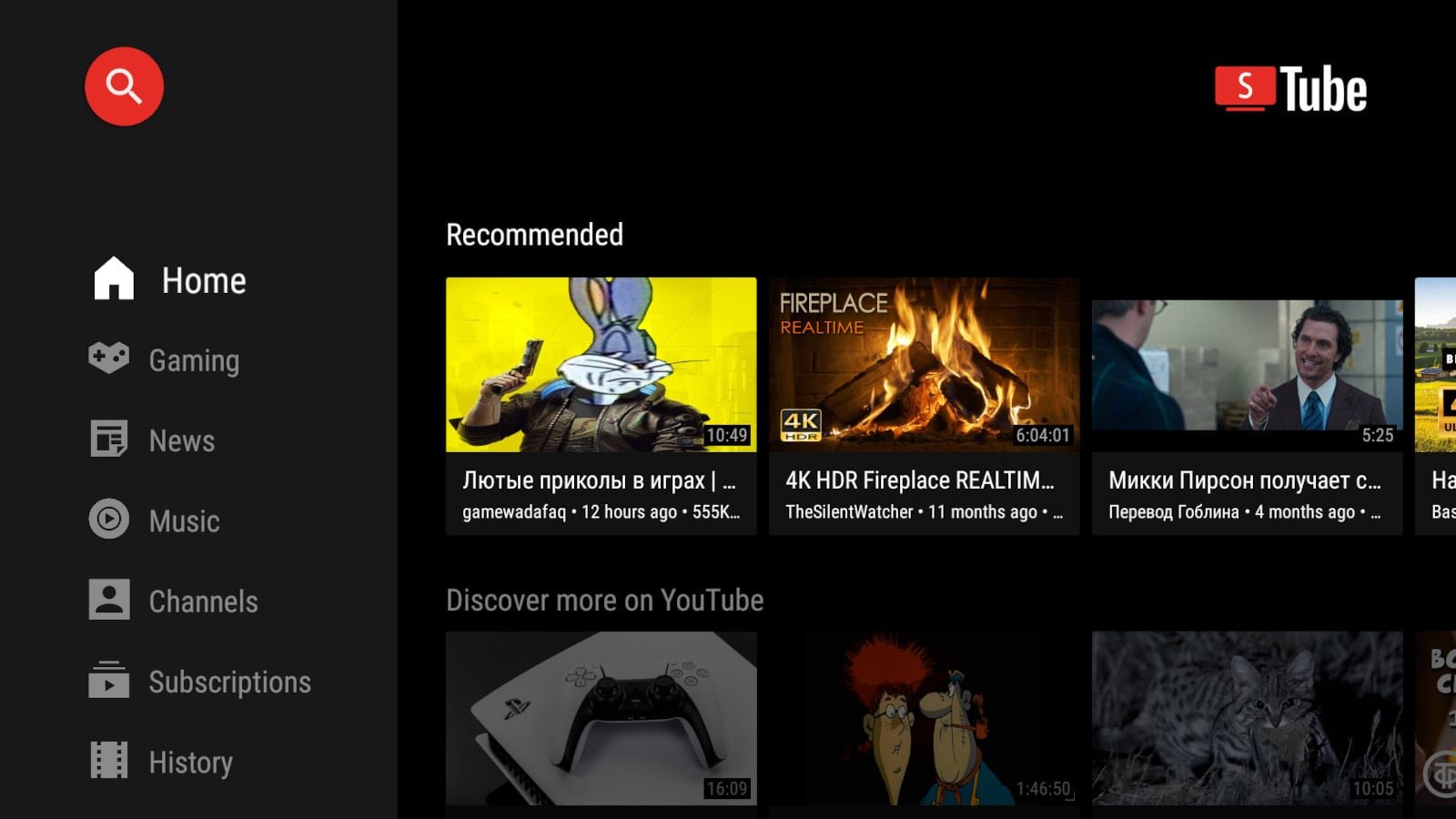
The recent security breach involving SmartTube, the widely-used open-source YouTube client for Android TV, has raised significant concerns among its user base. An attacker managed to gain access to the developer’s signing keys, which resulted in a malicious update being distributed to users. This incident came to light when numerous users reported that Play Protect, the built-in antivirus feature of Android, flagged SmartTube as a potential threat, prompting warnings about the app’s safety.
Developer’s Response and User Recommendations
Yuriy Yuliskov, the developer behind SmartTube, acknowledged the compromise of his digital keys late last week. In response, he revoked the old signature and announced plans to release a new version of the app with a distinct app ID, urging users to transition to this updated version as soon as it becomes available.
SmartTube has gained popularity due to its free access, ad-blocking capabilities, and efficient performance on devices with limited processing power. However, the recent incident has cast a shadow over its reputation. A user who reverse-engineered the compromised version, identified as number 30.51, discovered a hidden native library named libalphasdk.so. This library, which is not part of the public source code, was found to be injected into the app’s release builds.
Yuliskov expressed his concerns on a GitHub thread, stating, “Possibly a malware. This file is not part of my project or any SDK I use. Its presence in the APK is unexpected and suspicious. I recommend caution until its origin is verified.” The library operates silently in the background, collecting device fingerprints, registering with a remote backend, and periodically sending metrics and configuration data through an encrypted channel—all without any visible signs to the user.
While there is currently no evidence linking the malware to account theft or involvement in DDoS attacks, the potential for such activities remains a pressing concern. Although Yuliskov has announced the availability of safe beta and stable test builds on Telegram, these versions have yet to be uploaded to the official GitHub repository. Furthermore, the lack of detailed information regarding the breach has led to trust issues within the community.
Yuliskov has committed to addressing all user concerns in a comprehensive post-mortem once the new app is officially released on the F-Droid store. In the meantime, users are advised to remain on older, verified builds, refrain from logging in with premium accounts, and disable auto-updates to mitigate risks. Additionally, impacted users should consider resetting their Google Account passwords, reviewing their account activity for unauthorized access, and removing any unfamiliar services.
As the situation unfolds, the timeline of the breach and the specific versions of SmartTube that remain secure are still unclear. One user noted that version 30.19 does not trigger Play Protect warnings, suggesting it may be a safer option for those concerned about the recent developments. BleepingComputer has reached out to Yuliskov for clarification on which versions were affected, but a response has yet to be received.