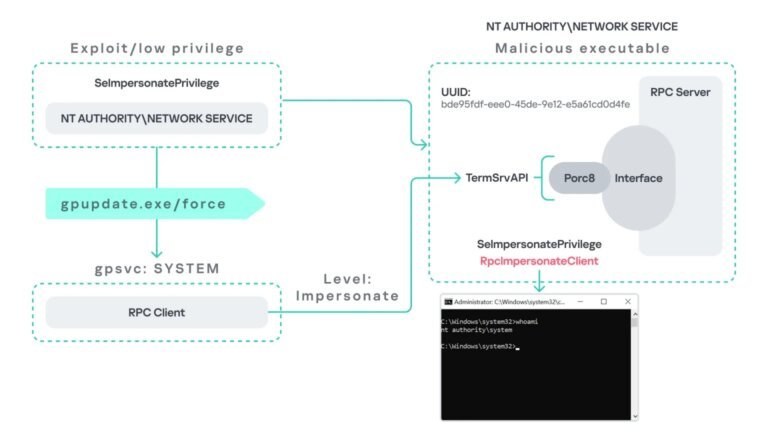
PhantomRPC is a significant architectural vulnerability in the Windows Remote Procedure Call (RPC) framework that allows local privilege escalation to SYSTEM-level access across all Windows versions. Discovered by Kaspersky's Haidar Kabibo at Black Hat Asia 2026, this vulnerability stems from the RPC runtime's failure to verify the legitimacy of a responding server during calls to offline or disabled servers. Attackers can exploit this by setting up a malicious RPC server that impersonates a legitimate endpoint, using the RpcImpersonateClient API to escalate privileges from low-privileged accounts to SYSTEM or Administrator levels.
Five distinct exploitation paths have been identified:
1. gpupdate.exe coercion: An attacker can intercept an RPC call made by the Group Policy Client service when executing gpupdate /force, granting SYSTEM-level access if TermService is disabled.
2. Microsoft Edge startup: Launching msedge.exe triggers an RPC call to TermService, allowing privilege escalation from Network Service to Administrator via a spoofed endpoint.
3. WDI background service: The Diagnostic System Host polls TermService regularly, enabling an attacker to exploit this without user interaction.
4. ipconfig.exe and DHCP Client: Running ipconfig.exe initiates an RPC call to the DHCP Client service, allowing a Local Service attacker to elevate privileges if DHCP is disabled and a fake server is present.
5. w32tm.exe and Windows Time: An attacker can expose a named pipe endpoint, allowing them to impersonate any privileged user executing the Windows Time executable.
The vulnerability was reported to Microsoft on September 19, 2025, but Microsoft categorized it as moderate severity and closed the case without a patch, as the attack requires SeImpersonatePrivilege, which is granted by default to certain accounts. Organizations are advised to implement defensive measures such as enabling RPC monitoring, ensuring legitimate services are running, and restricting SeImpersonatePrivilege. Kaspersky has provided tools for auditing environments for exploitable RPC call patterns through the PhantomRPC GitHub repository.