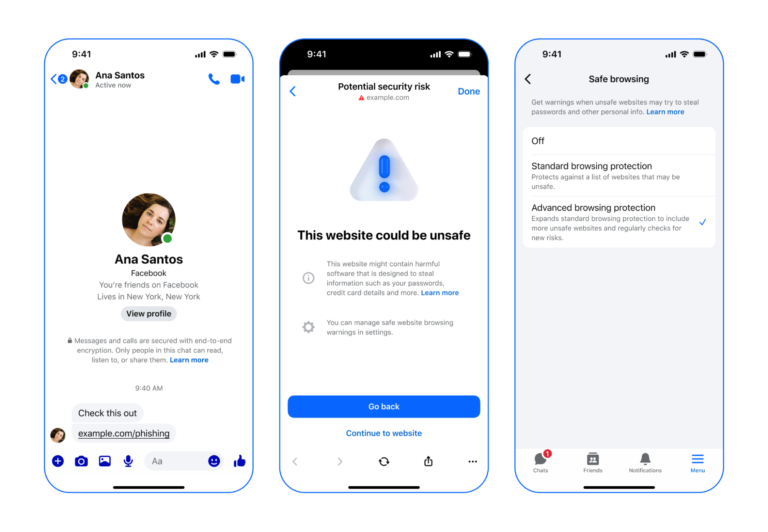
Advanced Browsing Protection (ABP) in Messenger enhances user privacy by warning users about potentially harmful links shared in end-to-end encrypted communications. It analyzes links using on-device models and a dynamic watchlist of millions of potentially malicious sites, utilizing cryptographic techniques to maintain user privacy.
ABP is based on a cryptographic primitive called private information retrieval (PIR), which minimizes the information a server learns from client queries. The system also employs oblivious pseudorandom functions (OPRFs) and manages URL queries through a privacy-preserving URL-matching scheme. The server groups links by domain, allowing clients to request a single bucket for domain-specific path components, and generates a ruleset to balance bucket sizes.
To safeguard client queries, AMD's SEV-SNP technology creates a confidential virtual machine (CVM) that processes hash prefixes securely, generating attestation reports for integrity verification. The use of Oblivious RAM and Oblivious HTTP (OHTTP) enhances privacy by preventing exposure of memory access patterns and stripping identifying information from client requests.
The lifecycle of an ABP request includes pre-processing phases where the server updates the URL database and computes rulesets, followed by client requests that involve calculating bucket identifiers, sending encrypted requests through a proxy, and checking for unsafe URLs based on server responses.