Bitdefender Total Security offers real-time malware and virus detection, multi-layer ransomware protection, a limited daily data VPN, a password manager, parental controls, and webcam protection. It is compatible with Windows, Mac, Android, and iOS. Pros include excellent detection ratings, minimal system impact, and coverage for up to five devices. Cons are a VPN data cap unless upgraded, significant renewal price increases, and some advanced features being buried in menus.
Surfshark Antivirus provides real-time malware scanning, webcam and microphone protection, data breach alerts, and is bundled with Surfshark VPN. It is available on Windows and Android. Pros include competitive pricing when bundled with VPN, a clean interface, and decent malware detection. Cons are fewer features compared to dedicated suites, limited iOS support, and being relatively new in the antivirus space.
Norton 360 includes real-time threat detection, LifeLock identity monitoring (on higher tiers), a built-in VPN with no data cap, cloud backup, and a password manager. It supports multiple platforms. Pros are strong overall protection, dark web monitoring alerts, and no VPN data limits. Cons include a higher starting price, automatic renewal enabled by default, and being resource-heavy on older machines.
Avast Free Antivirus offers real-time virus and malware protection, a Wi-Fi network scanner, a browser cleanup tool, and a basic ransomware shield. It is available on multiple platforms. Pros include core protection for free, lightweight installation, and an extensive threat database. Cons are aggressive upselling, past privacy concerns, and advanced features locked behind a subscription.
Malwarebytes focuses on malware and adware detection, offering real-time protection (Premium only), a browser guard extension, and a light system footprint. It is available on multiple platforms. Pros include excellent detection of adware and a user-friendly interface. Cons are the lack of real-time protection in the free version and fewer features compared to full-suite competitors.
Free antivirus software should prioritize real-time protection, coverage beyond basic viruses, a browser extension for blocking suspicious sites, and automatic updates. Free versions typically handle common threats adequately but lack advanced features and support found in paid versions. Some free tools may collect user data, raising privacy concerns.
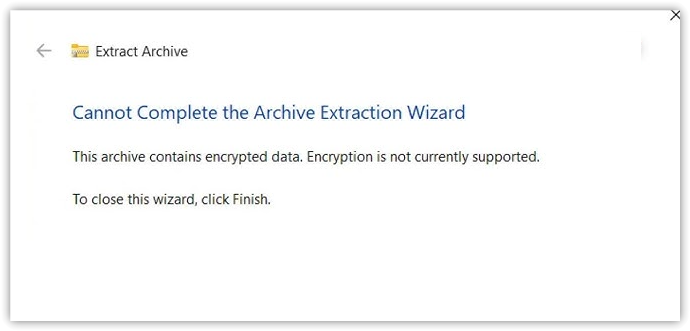
To install antivirus software on Windows 10, download it from the official website, follow setup instructions, and ensure background protection and automatic updates are enabled. Transitioning from Windows Defender is usually managed automatically by most antivirus programs.
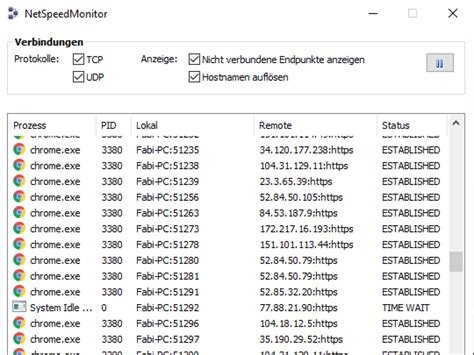
Running two real-time scanners can cause conflicts; instead, pair a primary antivirus with a secondary tool like Malwarebytes for manual scans. If a paid antivirus plan is not renewed, protection may revert to a limited mode or cease entirely. Microsoft Defender offers adequate protection but lacks additional features like a VPN or identity monitoring. Standard antivirus plans typically range from to 0 annually, with renewal prices often increasing.