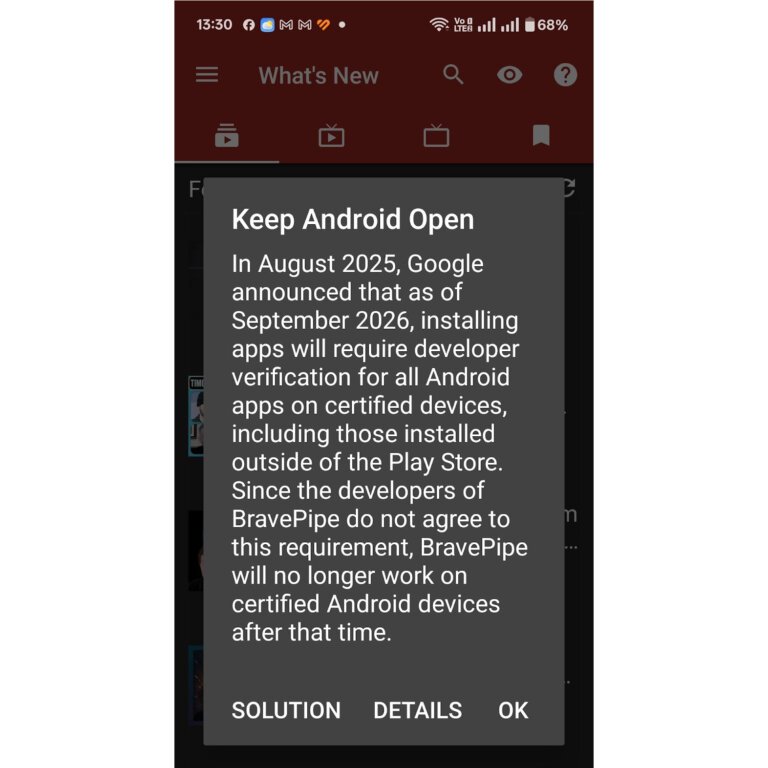
Google has updated the method for side-loading apps on Android devices to enhance user safety. Users must first enable Developer Mode in their settings. After this, they will be prompted to confirm if they are being guided through the process. There will be a delay before side-loading can begin, requiring a device reboot and a one-day waiting period to prevent scams. Users must then verify their identity using biometrics or a PIN. Finally, they can choose to enable side-loading for one week or permanently, with the latter option exempting them from future reauthorization.