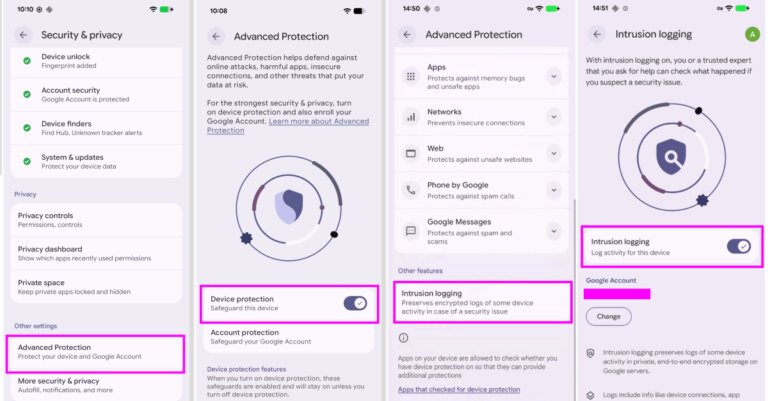
Google introduced a new opt-in feature for Android users called Intrusion Logging, which enhances the analysis of spyware attacks as part of the Advanced Protection Mode. Developed with Amnesty International and Reporters Without Borders, it logs daily device and network activities, including app activity, installations, network connections, file transfers, system certificate modifications, and device lock events. The log data is encrypted and stored securely, accessible only to the device owner. Logs are retained for 12 months and cannot be deleted by users before expiration, though they can be downloaded for offline storage. Intrusion Logging also records network events during Chrome's Incognito mode. This feature is beneficial for high-risk individuals who may be targets of surveillance. Users can access the logs through the Settings app, and the rollout is underway for devices with the Android 16 December update and newer.
Additionally, Google announced other privacy and security features, including a verified financial call feature to combat scams, expansion of Live Threat Detection, evaluation of APK files for malware, revocation of accessibility services API access from non-designated apps, and enhancements to Find Hub's Mark as Lost feature. Other updates include improved device recovery options, enhanced privacy controls, introduction of AISeal with pKVM, expansion of Binary Transparency, protection against OTP theft, and strengthening data protection with post-quantum cryptography.