Google has introduced a new mechanism called Advanced Flow within Android to facilitate the sideloading of APKs from unverified developers for power users while enhancing security. This system will launch in August and aims to balance user flexibility with protection against malware and scams, which caused losses of approximately billion last year.
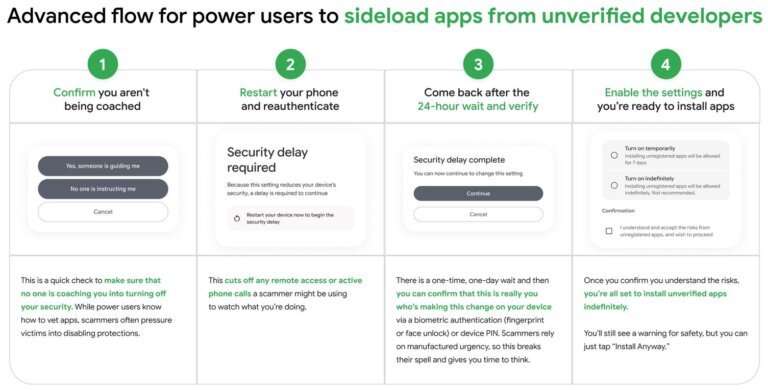
To install APKs from unverified developers, users must complete a one-time process that includes activating Developer Mode, confirming they are not influenced by threat actors, restarting the device, and verifying the legitimacy of modifications after a day. Once completed, users can install applications from unverified developers and choose to enable them for a week or indefinitely, with Android providing a warning about the unverified source.
The Advanced Flow process is designed to prevent users from being coerced into installing malicious software during scam attempts. Google emphasizes that this system is a compromise between Android's openness and necessary user protections, leading to upcoming developer verification requirements. All Android app publishers will need to undergo identity verification by Google, with non-compliance resulting in blocked software installations on certified Android devices. This verification initiative is now set for rollout in August 2026.