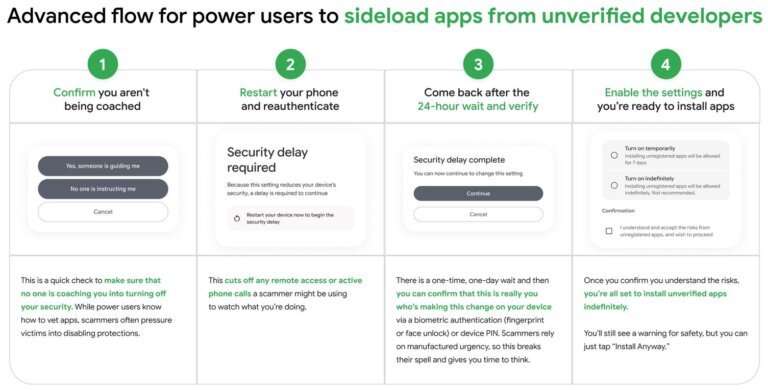
Android has implemented new sideloading rules that affect app installations outside the Play Store, complicating access for developers and users. F-Droid, a third-party app store, is particularly critical of the new verification requirements, which may force alternative stores to comply with Google's standards, potentially confusing users. Retro gaming emulators, often hosted on platforms like GitHub, may face barriers due to these rules, impacting user access to innovative tools. Smaller, privacy-focused encrypted messaging apps could struggle with the new verification process, complicating installation for users in high-risk environments. The modding community may see a decline in available tools as hobbyist developers resist compliance. Practical applications like Termux and Bromite may also face barriers, affecting user experience. While the changes may not be overly restrictive for average users, they introduce complexity that could deter power users and slow the adoption of non-Play Store applications.