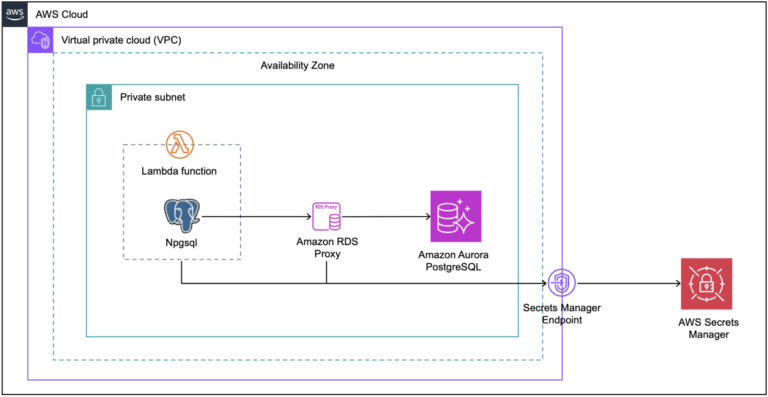
Many organizations are modernizing legacy .NET applications while reducing database costs and enhancing scalability, particularly during migrations to AWS Lambda and transitions from SQL Server to Amazon Aurora PostgreSQL-Compatible Edition. The process involves connecting Lambda functions to Aurora PostgreSQL using Amazon RDS Proxy, with AWS Secrets Manager managing secure credential storage. The architecture includes a .NET Lambda function interfacing with Aurora PostgreSQL via RDS Proxy, which provides connection pooling to minimize database connection overhead. The solution requires a CloudFormation template to provision resources such as a VPC with private subnets, an Aurora PostgreSQL cluster, RDS Proxy, and Secrets Manager.
The RDS Proxy is configured with parameters including PostgreSQL engine family, idle client connection timeout, and Secrets Manager secret. A Windows EC2 instance is provisioned, and access is facilitated through AWS Systems Manager Fleet Manager. The solution includes creating a sample table named "employee" in the database and a new .NET Lambda project that utilizes Npgsql for database connections. The Lambda function is deployed using the AWS CLI, and testing involves invoking the function and retrieving logs from Amazon CloudWatch. Finally, resources created during the process should be deleted to prevent ongoing charges.