A newly identified Android malware called BeatBanker disguises itself as a Starlink application on fake Google Play Store websites. It functions as a banking trojan and includes Monero mining capabilities, allowing it to steal credentials and manipulate cryptocurrency transactions. Researchers at Kaspersky traced BeatBanker to campaigns targeting users in Brazil. The latest version uses the BTMOB RAT for remote access, enabling keylogging, screen recording, camera access, GPS tracking, and credential capture.
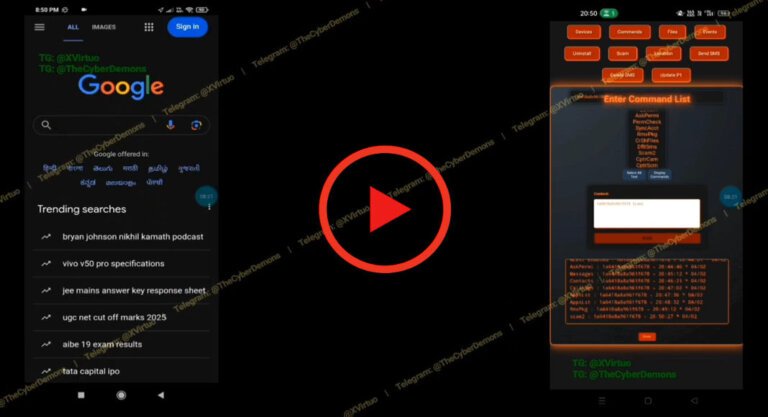
BeatBanker is distributed as an APK file that decrypts and loads hidden code into memory, conducting environment checks before activation. It presents a fake Play Store update screen to trick users into granting permissions for additional payloads. To avoid detection, it delays malicious operations and plays a nearly inaudible MP3 file to maintain persistent activity.
The malware uses a modified version of the XMRig miner to mine Monero on Android devices, connecting to mining pools through encrypted TLS connections. It can start or stop mining based on device conditions and uses Firebase Cloud Messaging to relay device information to its command-and-control server. Currently, BeatBanker infections have only been observed in Brazil, but there are concerns about its potential spread. Users are advised to avoid side-loading APKs from untrusted sources and to review app permissions regularly.