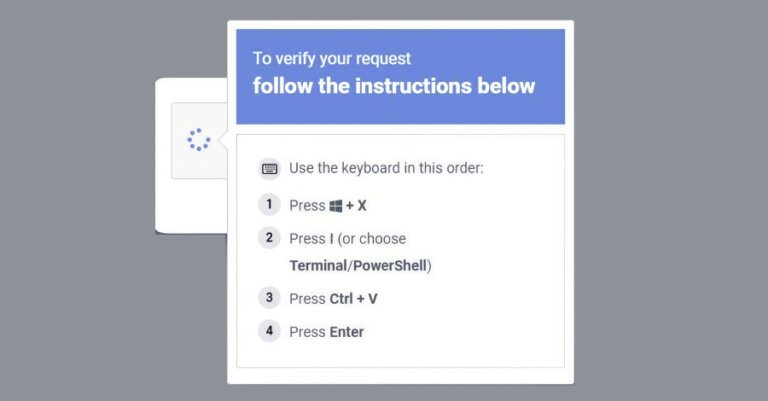
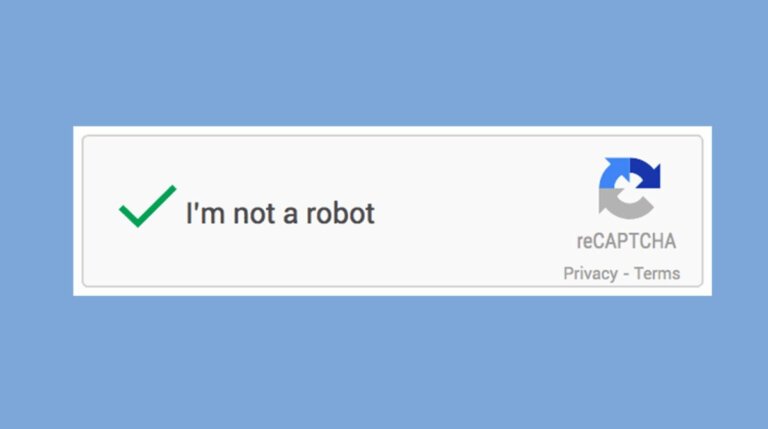
Vancouver-based developer Sunset Visitor has announced its new project, Prove You're Human, during the Triple-i showcase. In this game, players take on the role of a digital copy of a person testing a corporate product called Mesa, a robotic AI that believes it is human. The objective is to convince Mesa of her artificiality while exploring themes of identity and existence. The game features a vibrant virtual world and unique interactions, including a twist on the CAPTCHA test. Players face a choice at the climax: to merge back with their real-life counterpart or embrace digital existence. A release date has not been announced, but anticipation is growing.