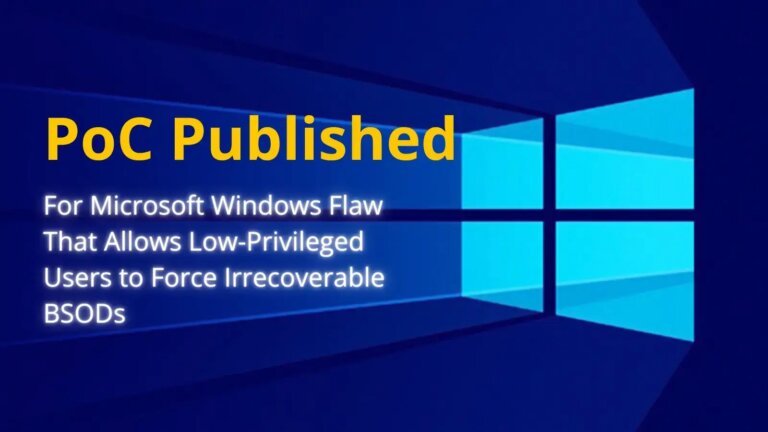
AI-powered fileless malware poses a significant challenge to Windows 11 security, as traditional antivirus solutions struggle to detect these advanced threats. This type of malware operates without traditional files and can execute malicious actions directly in memory, bypassing conventional detection methods. Vulnerabilities in applications like Excel and Outlook have been exploited, allowing harmful code execution through simple actions like opening a preview pane. The integration of AI features, such as Microsoft's Copilot, has also created new risks, leading to potential data leaks. To combat these threats, a multi-layered security approach that includes behavioral analysis and real-time monitoring is essential. Upgrading from Windows 11 Home to Windows 11 Pro provides additional security features to enhance defenses against malware.