Folder permissions in Windows 11 control access to files, determining who can read, modify, or delete them. Common issues arise from drive or file migration, Windows updates, malware, or user errors. Symptoms include "Access Denied" messages and ownership displayed as "unknown."
Methods to resolve folder permission issues include:
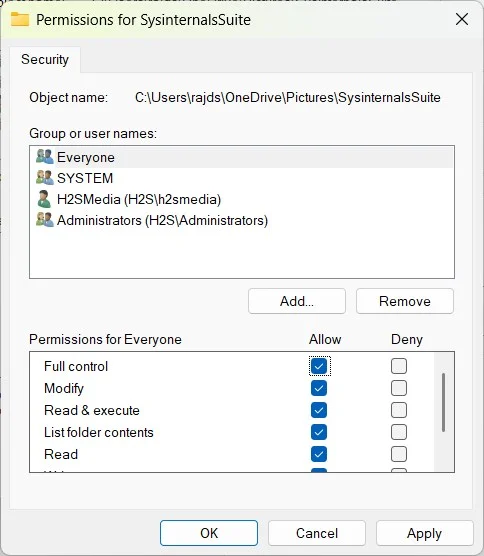
1. Security Tab: Reset permissions through the Security tab by modifying access levels and ensuring proper inheritance.
2. Take Ownership: Claim ownership of a folder if the current owner is no longer valid, then reset permissions.
3. Command Prompt: Use commands like PLACEHOLDERfa5c045a85bc6cf0 and PLACEHOLDER14a87b7576573f58 to reset permissions quickly and efficiently.
4. PowerShell: Utilize PowerShell for advanced permission resets, allowing for conditional logic.
5. Windows Reset: As a last resort, reset Windows to restore default permissions while keeping personal files.
To prevent future issues, back up permissions before changes, understand NTFS vs. share permissions, and avoid altering system folders. If problems persist, ensure commands are run as an administrator, check ownership settings, and verify that Group Policy or sync tools are not overriding changes.