A phishing campaign has been identified that uses a counterfeit Microsoft support website, microsoft-update[.]support, to trick users into downloading a malicious Windows update disguised as WindowsUpdate 1.0.0.msi. This file, created on April 4, 2026, appears legitimate but contains malware designed to steal sensitive information. The campaign targets French-speaking users, leveraging recent data breaches in France to create convincing scams.
The malware, once executed, installs an Electron application that runs a Python interpreter, which then deploys various data theft tools. It employs two persistence mechanisms: modifying the Windows registry and creating a shortcut in the Startup folder. The malware connects to external sites for reconnaissance and data exfiltration, using domains like datawebsync-lvmv.onrender[.]com and store8.gofile[.]io.
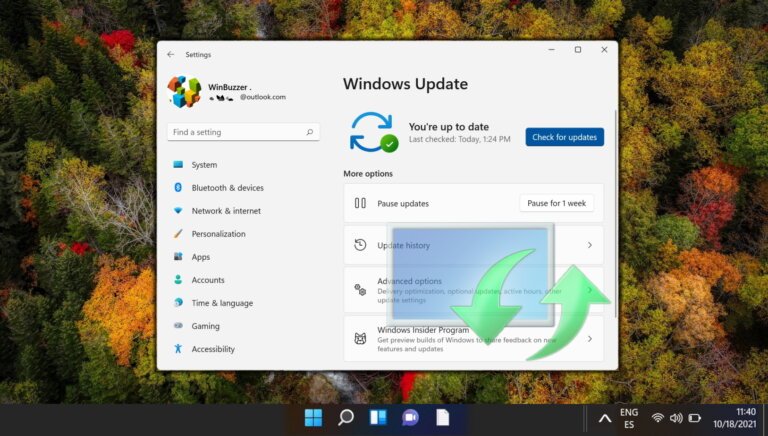
The malware's components have evaded detection by antivirus tools, with VirusTotal reporting zero detections for the main executable and its launcher. Users are advised to check their registry, remove suspicious files, change passwords, and run a full system scan if they suspect installation of the malicious update. Safe updating practices include using the built-in Windows update feature and being cautious of phishing attempts.
Indicators of compromise include specific file hashes, domains associated with the phishing campaign, and file system artifacts related to the malware's installation.