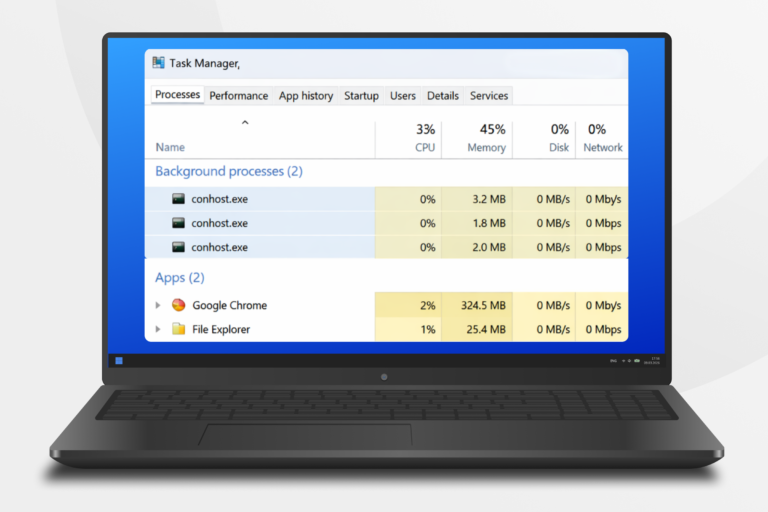
Conhost.exe, or Console Window Host, is a legitimate Windows system process responsible for managing the display and behavior of console windows such as Command Prompt and PowerShell. It facilitates text rendering and manages input/output interactions with the graphical user interface. Each time a console application is launched, a new instance of conhost.exe is created, and multiple instances can appear in Task Manager based on active console applications.
To verify the authenticity of conhost.exe, it should run from C:WindowsSystem32 or C:WindowsSysWOW64, have a valid Microsoft Windows Publisher digital signature, and not make outbound network connections. High CPU usage or unusual behavior may indicate malware masquerading as conhost.exe. Troubleshooting steps for issues related to conhost.exe include running a malware scan, checking for Windows updates, updating device drivers, and using the System File Checker. Disabling conhost.exe is not advisable as it is essential for the functioning of console applications.