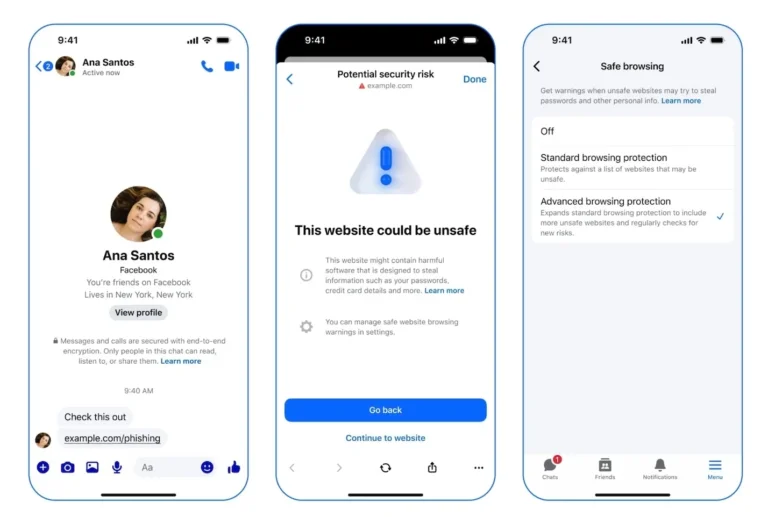
Microsoft will introduce phishing-resistant passwordless authentication through passkeys for Windows devices, integrated with Microsoft Entra. This feature is expected to enter public preview between mid-March and late April 2026 for global tenants, while government cloud environments will receive the update from mid-April to mid-May. Users can access Entra-protected resources using device-bound passkeys stored securely within Windows Hello, allowing authentication through biometric or local verification methods. This update expands passwordless authentication to unmanaged or personal Windows devices. Passkeys utilize public-key cryptography, enhancing security by storing a private key on the device and registering a matching public key with the service. Each passkey is uniquely associated with a specific device and cannot be exported or synchronized. Organizations must enable the Passkeys (FIDO2) authentication method in Entra for the preview. This initiative is part of Microsoft's broader strategy to eliminate passwords, responding to rising cybersecurity concerns related to password-based authentication.