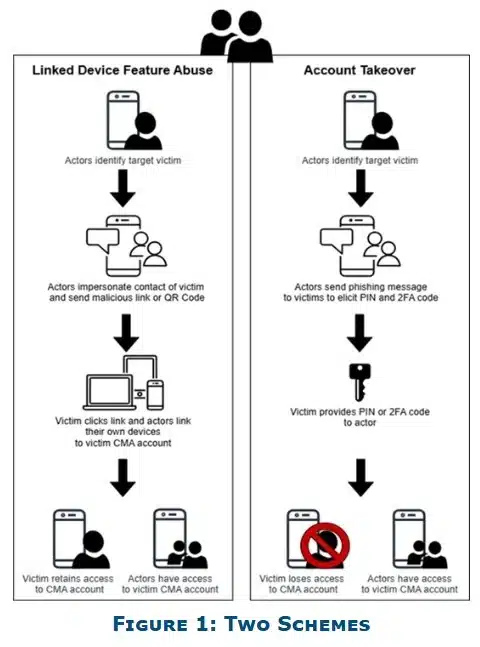
A phishing campaign targeting users of messaging applications has been reported by the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI). This campaign exploits human behavior rather than software vulnerabilities, leading to the compromise of thousands of accounts worldwide, despite encryption. Attackers impersonate official support accounts and use social engineering tactics to prompt users to click on malicious links, request verification codes, or suggest account recovery actions. If users comply, attackers can take control of their accounts and may deploy malware. Platforms like Signal have been specifically targeted, but the tactics can apply to various messaging applications. Recommendations for users include being cautious with suspicious messages, avoiding unknown requests, carefully checking links, monitoring group chats for fake accounts, using built-in security features, and reporting incidents promptly.