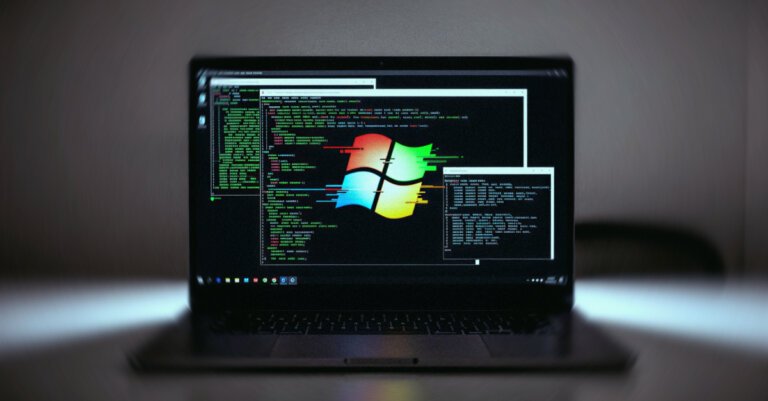
A malware operation called WeedHack has targeted Minecraft players since January, compromising over 116,000 systems with daily infections between 2,000 and 3,000. It primarily distributes malware through malicious mods, clients, cheats, and utilities promoted on YouTube, utilizing SEO poisoning to reach victims. The campaign features polished YouTube videos with embedded download links and targets keywords related to popular Minecraft clients. WeedHack operates as a malware-as-a-service (MaaS) model, offering a free tier that steals Minecraft session IDs, cookies, and passwords across various platforms, and a premium tier with enhanced capabilities. The operation's Telegram channel has over 800 members, mostly teenagers or young adults. Minecraft players are advised to trust only official sources for mods and verify download links to protect against these threats.