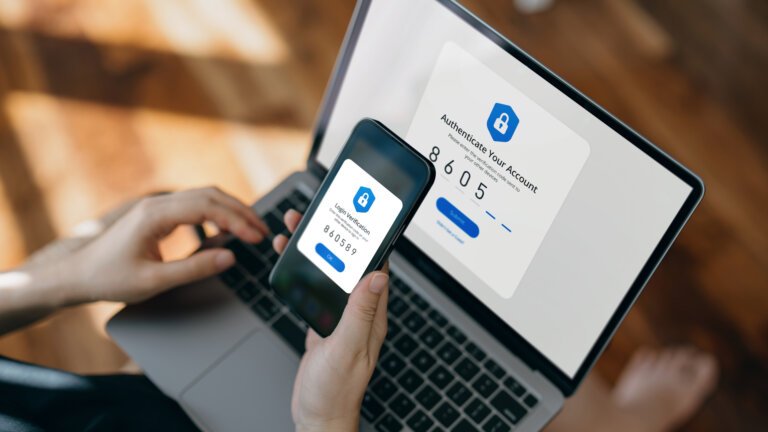
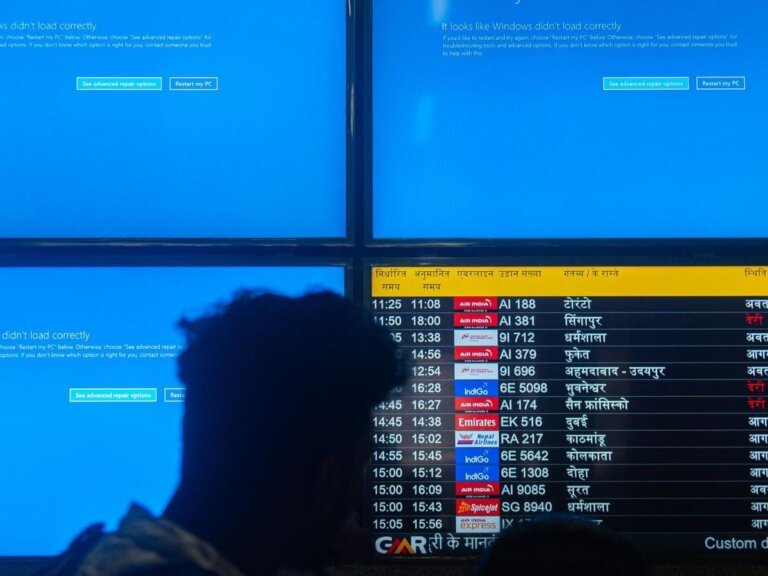
Residents and visitors in Morong, Rizal, and Mambajao, Camiguin Island can now make emergency calls through messaging apps and social media platforms as part of a modernization initiative for emergency response systems. Mambajao activated its local 911 emergency hotline on February 27, becoming the first next-generation 911-enabled command center in Northern Mindanao, reducing response times to three to seven minutes. The Next Generation Advanced (NGA) 911 Philippines launched the NEXiS Message platform, allowing emergency calls via traditional voice methods, text messages, video calls, and popular applications like Facebook Messenger. This system consolidates incoming messages into a single platform, improving efficiency and response times while ensuring the security of shared information through encryption. NEXiS Message integrates with legacy and modern communication technologies and facilitates inter-agency collaboration. NGA 911 Philippines aims to expand next-generation 911 technology to more communities in the country and has received certification from the National Emergency Number Association (NENA).