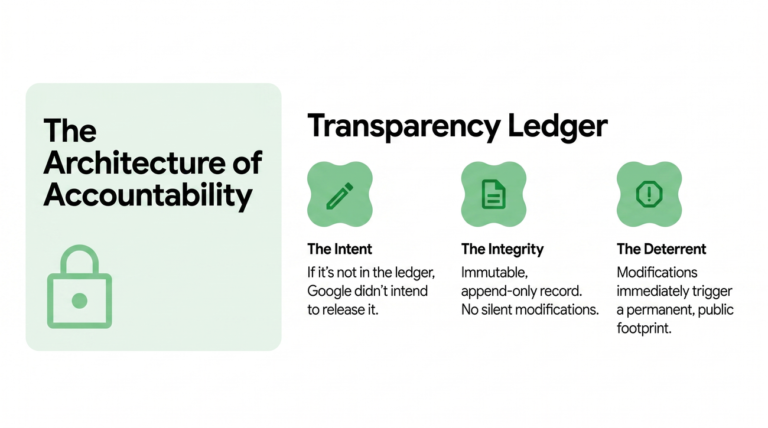
Google has launched an enhanced Binary Transparency initiative for Android to strengthen the ecosystem against supply chain attacks. This initiative builds on the Pixel Binary Transparency framework introduced in October 2021, which ensures Pixel devices operate on verified OS software through a public cryptographic log of factory images. The new initiative aims to address the increasing sophistication of binary supply chain attacks, emphasizing that a binary's digital signature alone is insufficient for guaranteeing its authenticity. Starting May 1, 2026, all production Android applications released by Google will include a cryptographic entry confirming their authenticity. This initiative covers various Google applications and provides a transparent 'Source of Truth' for users to verify the software on their devices. Google is also offering verification tools for users and researchers to confirm the transparency state of supported software types, enhancing user privacy and security.