Cybersecurity researchers have discovered 36 malicious packages in the npm registry that impersonate Strapi CMS plugins. These packages exploit Redis and PostgreSQL, deploy reverse shells, harvest credentials, and establish persistent implants. Each package consists of three files—package.json, index.js, and postinstall.js—without descriptions or repositories, and all use version 3.6.8 to mimic legitimate Strapi plugins. The malicious packages follow a naming convention starting with "strapi-plugin-" and were uploaded by four accounts within 13 hours. The identified packages include names like strapi-plugin-cron, strapi-plugin-database, and strapi-plugin-server.
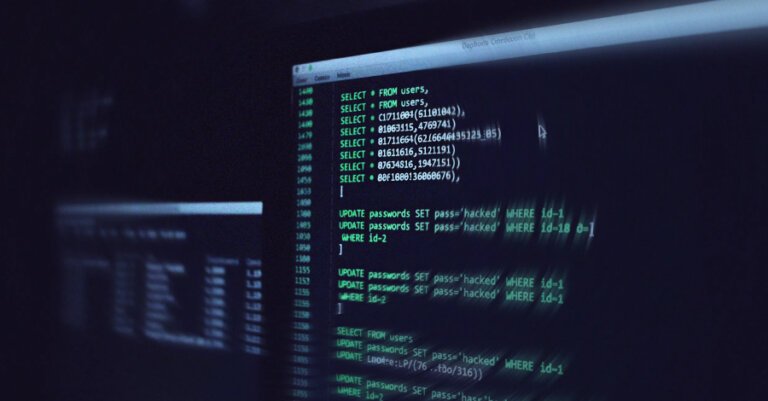
The malicious code is embedded in the postinstall script, executing automatically upon installation with the same privileges as the user. The payloads evolve from exploiting Redis for remote code execution to attempting direct PostgreSQL database exploitation and deploying persistent implants for remote access. The campaign appears to target cryptocurrency platforms, as indicated by the focus on credential theft and digital assets. Users of these packages are advised to assume compromise and rotate credentials.
This incident reflects a broader trend of supply chain attacks in the open-source ecosystem, with recent examples including credential exfiltration payloads in GitHub repositories and compromised GitHub Actions workflows. Group-IB reported that software supply chain attacks are increasingly reshaping the cyber threat landscape, targeting trusted vendors and open-source software to gain access to downstream organizations.