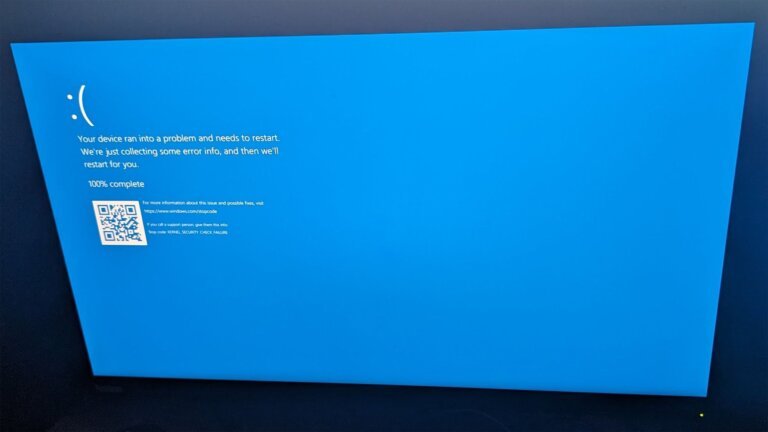
Microsoft is facing scrutiny due to a critical remote execution vulnerability, CVE-2026-41089, rated at 9.8, affecting Windows Server domain controllers from version 2012 onward. This vulnerability allows unauthenticated users on the same network to send malformed UDP packets to a domain controller, potentially granting unauthorized system access or causing a reboot, leading to denial-of-service scenarios. The vulnerable service is Netlogon, and there are no immediate mitigations available; patches will be released on May 12. The vulnerability could allow attackers to create multiple accounts with various access levels, compromising the security of entire networks. Cybersecurity experts recommend patching all linked domain controllers simultaneously. The vulnerability is caused by a buffer overflow in the Netlogon service due to a field in a network packet exceeding its expected size. A GitHub repository exists with proof-of-concept code that can crash the LSASS service. Additionally, Microsoft is in conflict with security researcher Chaotic Eclipse, who has published zero-day exploits following a breakdown in negotiations.