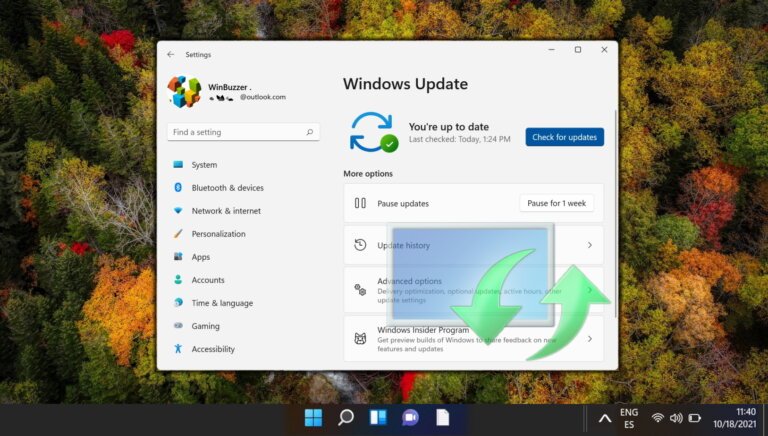
Microsoft's April 2026 Windows security update, KB5083769, may disrupt image-mount operations for backup applications such as Macrium Reflect, Acronis Cyber Protect Cloud, UrBackup Server, and NinjaOne Backup due to the addition of the psmounterex.sys kernel driver to its Vulnerable Driver Blocklist. This action was taken to address a high-severity buffer overflow vulnerability, CVE-2023-43896. The inclusion of this driver in the blocklist has rendered several backup products inoperable, and Microsoft will not retract the block for security reasons. Administrators can use Event ID 3077 in the Code Integrity log to confirm that the blocklist is causing the failures. Microsoft advises updating backup applications to versions that include necessary driver protections instead of uninstalling or pausing the security patch. Additionally, the April updates have caused other issues, such as failures in Windows Server installations and devices booting into BitLocker recovery mode.