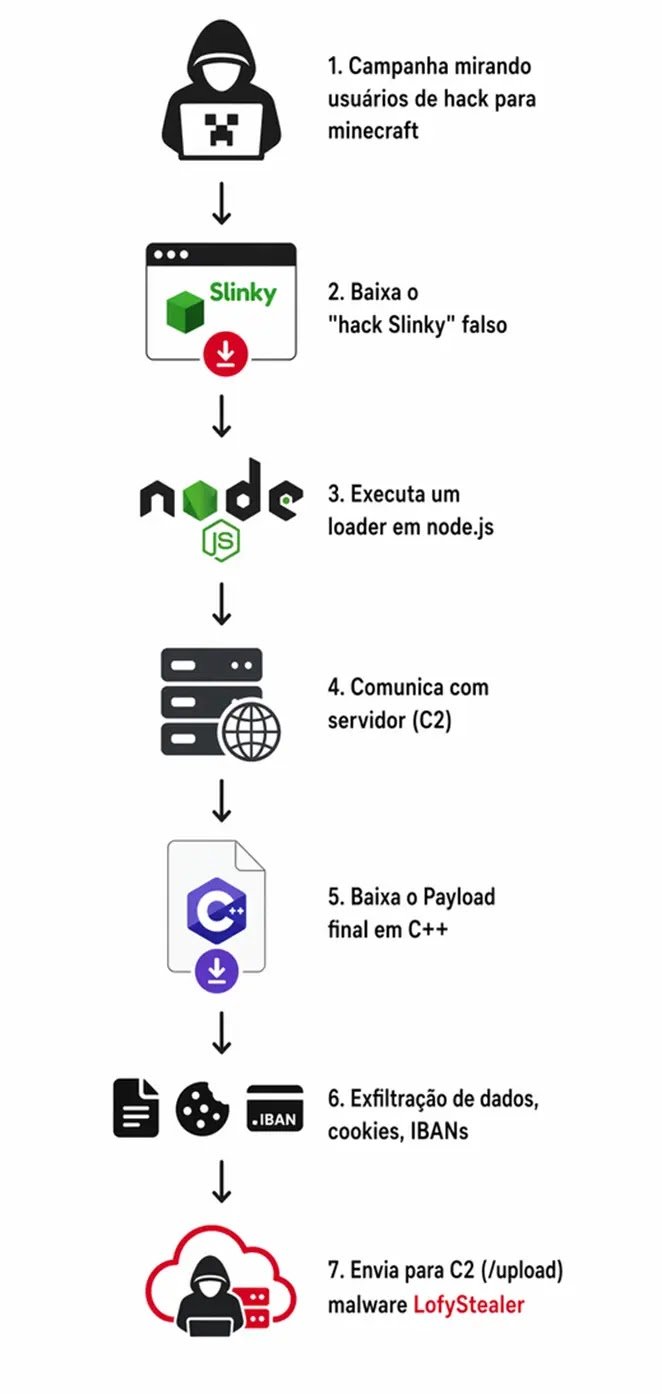
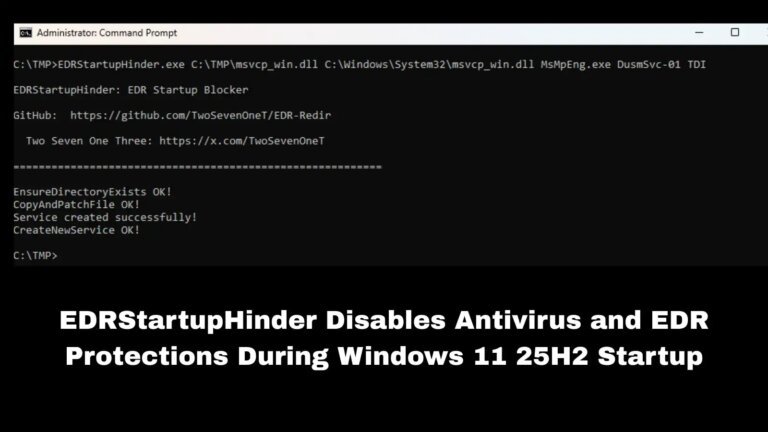
Cybersecurity threat hunters have discovered an active infostealer campaign targeting the gaming community, involving malware called LofyStealer (or GrabBot) that disguises itself as a Minecraft hack named “Slinky.” The attackers use the official game icon to trick young gamers into executing the malware. The Brazilian cybercrime group LofyGang has enhanced its technical capabilities, utilizing a sophisticated two-stage modular architecture. The initial stage features a 53.5 MB loader file named load.exe, which is a Node.js runtime environment that obscures malicious signatures. The loader connects to the attacker’s server and decrypts a 1.4 MB C++ payload, chromelevator.exe, which targets eight web browsers to extract sensitive information like cookies and passwords. The stolen data is compressed, encrypted, and sent to the attacker’s server. LofyGang has evolved into a Malware-as-a-Service platform, offering a web panel for operators to monitor victims and generate custom executables. The campaign highlights the increasing threats to the gaming community, with advanced evasion techniques being employed by cybercriminals. Security professionals are advised to monitor network traffic and conduct audits for suspicious activities.