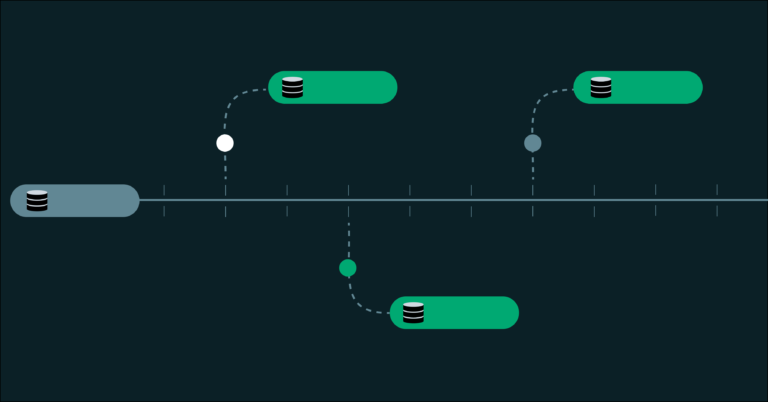
Support for OrientDB in Sonatype Nexus Repository has been discontinued, and older versions of Nexus Repository (prior to 3.70.5) are built on an outdated architecture that presents high-severity vulnerabilities and cannot be fully patched. The recommended database for Nexus Repository is now PostgreSQL, which offers better performance and support for modern architectures. Users have two migration options: transition to Sonatype Nexus Repository Cloud, which is fully managed and eliminates database management, or migrate to PostgreSQL while maintaining a self-hosted environment, which requires ongoing maintenance and infrastructure ownership.