Recent findings have identified a vulnerability in fully patched Windows 11 systems that allows attackers to install custom rootkits, which can bypass endpoint security and maintain persistence on compromised systems. This vulnerability is linked to a downgrade attack technique demonstrated by SafeBreach researcher Alon Leviev at Black Hat USA 2024, using an exploit tool called Windows Downdate. This tool enables an attacker with administrative access to manipulate the Windows Update process, reverting patched components to vulnerable states.
Leviev's demonstration showed that even systems using virtualization-based security (VBS) are at risk, as he could downgrade VBS features and expose previously fixed privilege escalation vulnerabilities. Microsoft has patched two vulnerabilities (CVE-2024-21302 and CVE-2024-38202) but has not addressed the core issue of the downgrade capability. Microsoft maintains that the ability for an admin-level user to gain kernel code execution does not cross a security boundary.
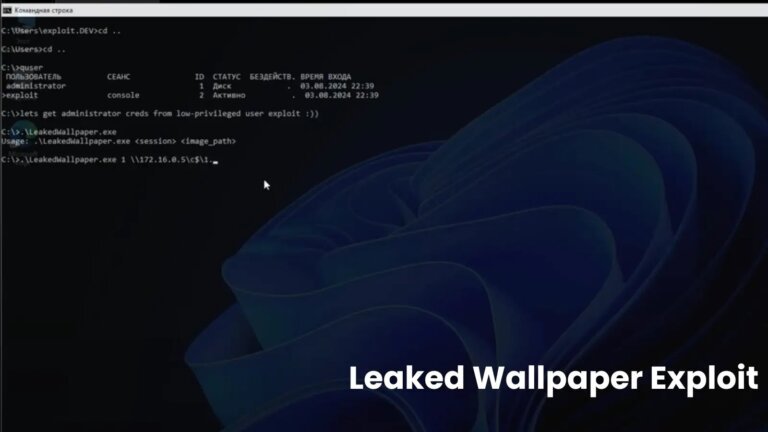
Leviev released details of a new downgrade attack on October 26, using the Windows Downdate tool to revive a driver signature enforcement bypass attack. He categorized this flaw as False File Immutability (FFI), exploiting incorrect assumptions about file immutability. He noted that downgrading specific OS modules, like CI.dll, allows exploitation even with VBS enabled. Tim Peck from Securonix highlighted that the attacks exploit Windows' failure to validate DLL version numbers properly, enabling the use of outdated, vulnerable files.
Microsoft is actively developing mitigations against these risks, including a security update to revoke outdated VBS system files, although specific measures and timelines are not yet disclosed.