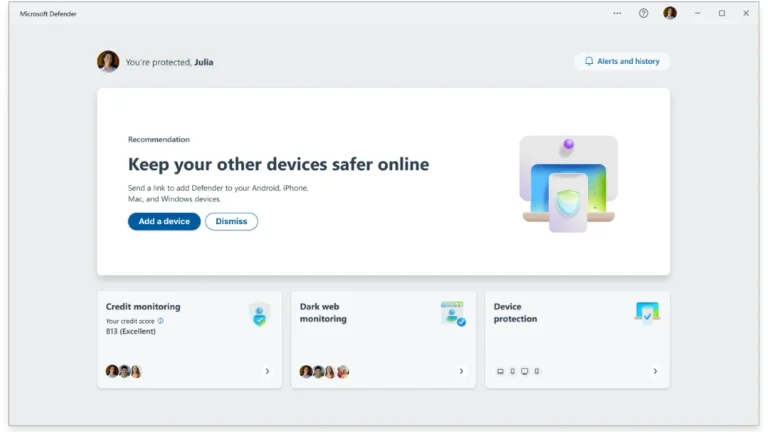
Windows 11 includes Microsoft Defender Antivirus, which is active from the moment the device is powered on and integrated into the operating system. It continuously updates to protect against various threats, including malicious files and unsafe links. Microsoft Defender SmartScreen evaluates the safety of websites and downloads, providing warnings for dubious content. Smart App Control prevents untrusted applications from executing, while Controlled folder access protects personal files from unauthorized modifications. Users can verify the operational status of Microsoft Defender Antivirus through Windows Security settings. Best practices for maintaining security include keeping the antivirus updated, using a single real-time antivirus engine, and enhancing security habits. Microsoft Defender Antivirus is generally sufficient for everyday risks, but additional third-party antivirus solutions may be considered based on individual needs.