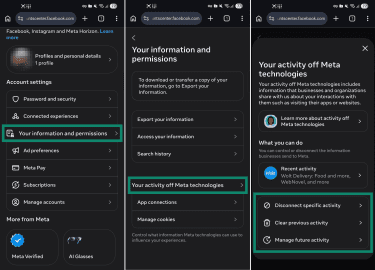
Meta AI has been integrated into Facebook, Instagram, WhatsApp, and Messenger, enhancing user experiences with features like search functionalities, chat interactions, and content generation. Users express a desire to limit their interactions with Meta AI due to concerns about transparency, privacy, and data security. The AI model is trained on diverse data sources, including public posts and user interactions, raising issues regarding data control. On WhatsApp, personal messages and calls are end-to-end encrypted, while Instagram may share past messages with Meta AI for context. Security vulnerabilities have been reported, including incidents of data mishandling. Currently, there is no comprehensive option to disable Meta AI across all platforms, but users can take steps to limit interactions, such as muting AI prompts and adjusting privacy settings. Users in the E.U. and U.K. can object to certain data uses under GDPR by submitting requests through their Meta accounts. To protect privacy, users are advised to opt out of AI training, limit personal data sharing, and use privacy tools like VPNs.