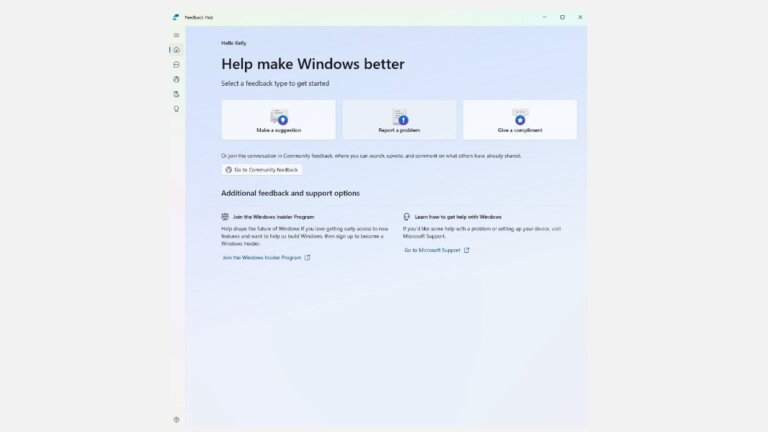
Windows 11's taskbar has faced criticism for its lack of customization options, prompting the development of a tool called Windhawk. Windhawk allows users to customize the taskbar extensively, including options for translucency and styles reminiscent of Windows XP and Vista. It features a "Taskbar Clock Customization" mod that displays CPU and RAM usage on the taskbar, and a "Taskbar on top for Windows 11" mod that enables users to move the taskbar to the top of the screen. The "Taskbar Volume Control" mod turns the entire taskbar into a volume control area, while the "Middle click to close on the taskbar" mod allows users to close applications with a middle-click. Additionally, the "Click on empty taskbar space" mod lets users set custom shortcuts for various actions. Windhawk also includes mods for adjusting thumbnail sizes, adding power buttons to the Start menu, and restoring the classic context menu, enhancing the overall user experience and functionality of the Windows 11 taskbar.