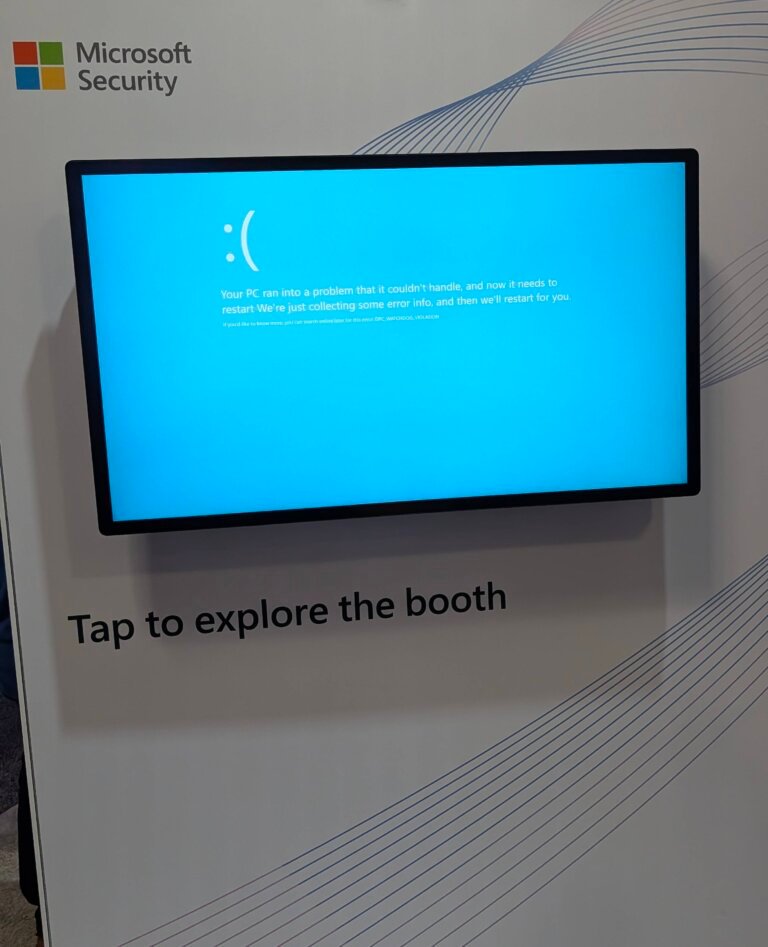
At the RSAC 2026 Conference, Microsoft showcased two screens displaying the Blue Screen of Death (BSOD), one resembling Windows 98 and the other Windows 8. The Windows 98 BSOD featured unusual hexadecimal values, suggesting it might not be a genuine error message. The Windows 8 screen displayed a message indicating a problem with the PC, raising questions about its authenticity. Microsoft has not clarified the intent behind these displays, which could either be a marketing strategy or a retrospective on Windows errors. The situation highlights the complexities of software reliability and user experience.