A pro-Russian hacktivist group, CyberVolk, has re-emerged in 2025 with a new ransomware-as-a-service (RaaS) operation called VolkLocker, which targets both Windows and Linux systems using Golang. The group utilizes Telegram bots for command-and-control operations, allowing affiliates to manage ransomware interactions. Despite its advancements, coding errors in the ransomware enable victims to recover encrypted files without paying a ransom. VolkLocker employs AES-256 encryption but has a critical flaw where the master encryption key is hard-coded and saved in plaintext, allowing easy decryption. The ransomware also ensures persistence by replicating itself and disabling essential system tools. CyberVolk offers additional RAT and keylogger add-ons for sale, with complete RaaS packages priced between [openai_gpt model="gpt-4o-mini" prompt="Summarize the content and extract only the fact described in the text bellow. The summary shall NOT include a title, introduction and conclusion. Text: A newly rebooted pro-Russian hacktivist group, CyberVolk, has made a notable comeback in 2025, unveiling a new ransomware-as-a-service (RaaS) operation dubbed VolkLocker, as detailed in recent research by SentinelOne.
After a prolonged period of dormancy following extensive bans on Telegram, this group has re-emerged with a Golang-based ransomware solution that targets both Windows and Linux systems. This latest initiative signifies CyberVolk's commitment to revitalizing its operations, showcasing what analysts refer to as the “CyberVolk 2.x” generation of tools.
Despite the group's advancements, their integration of sophisticated Telegram-based automation has inadvertently led to coding errors that allow victims to recover their encrypted files without the need to pay a ransom.
Telegram-Fueled Automation and Functionality
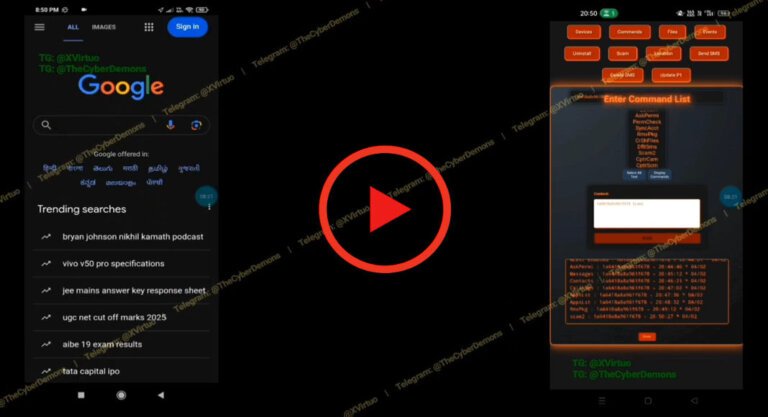
VolkLocker is heavily reliant on Telegram bots for its command-and-control operations, which form the core of its new RaaS model. All interactions between operators and the ransomware's ecosystem, from onboarding new customers to managing victims, are facilitated through a Telegram bot known as CyberVolk_Kbot.
This bot provides various commands such as /decrypt, /list, and /status, enabling affiliates to monitor infections and communicate with compromised systems in real time. Operators tasked with creating new ransomware payloads must input several configuration details, including a Bitcoin address, Telegram bot token ID, chat ID, encryption deadline, and file extension.
Decryption triggered via backed-up key file
This design approach aligns with CyberVolk’s goal of simplifying deployment for affiliates with limited technical skills. The Golang-based payloads, compiled for both Linux and Windows platforms, utilize the “ms-settings” UAC bypass technique (MITRE ATT&CK T1548.002) for privilege escalation. Once operational, VolkLocker performs system reconnaissance, checks for virtual machine environments by matching MAC address prefixes, and strategically excludes key system paths from encryption.
Encryption Flaws and System Destruction Features
VolkLocker employs AES-256 in Galois/Counter Mode (GCM) for file encryption; however, its encryption design reveals a significant oversight. The master encryption key is hard-coded within the binary and is also saved in a plaintext file named system_backup.key located in the %TEMP% directory. This easily accessible key allows victims to decrypt their files without paying the ransom, highlighting a critical flaw in CyberVolk’s development process.
In addition to its encryption capabilities, VolkLocker ensures persistence by replicating itself across multiple directories and disabling essential tools such as Task Manager, Windows Defender, and Command Prompt through registry modifications. It also deletes Volume Shadow Copies and can trigger a Blue Screen of Death (BSOD) using the Windows NtRaiseHardError() function when the countdown timer expires or when incorrect decryption keys are repeatedly entered.
Despite these coding missteps, CyberVolk is expanding its offerings, providing RAT and keylogger add-ons for 0 each, along with complete RaaS packages ranging from 0 to ,200. SentinelOne researchers caution that this resurgence underscores how politically motivated groups are increasingly leveraging Telegram infrastructure to commercialize their ransomware operations.
Indicators of Compromise:
Windows Sample: dcd859e5b14657b733dfb0c22272b82623466321
Linux Sample: 0948e75c94046f0893844e3b891556ea48188608
Bitcoin Wallet: bc1qujgdzl0v82gh9pvmg3ftgnknl336ku26nnp0vy
Telegram Bot: 8368663132:AAHBfe3xYPtg1IMynKhQy1BRzuF5UZRZspw
Find this Story Interesting! Follow us on Google News, LinkedIn, and X to Get More Instant Updates" max_tokens="3500" temperature="0.3" top_p="1.0" best_of="1" presence_penalty="0.1" frequency_penalty="frequency_penalty"] and ,200. Indicators of compromise include specific Windows and Linux sample hashes, a Bitcoin wallet address, and a Telegram bot ID.