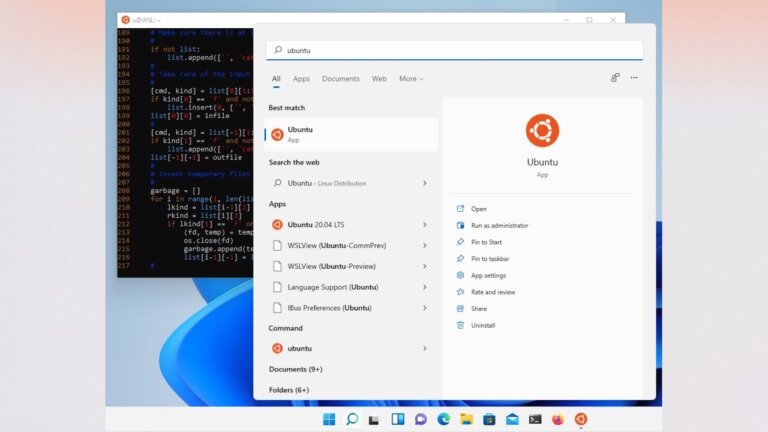
Microsoft has announced enhancements for the Windows Subsystem for Linux (WSL) to improve the experience for developers using Linux tools on Windows. Key areas of focus include:
- Faster file performance between Linux and Windows
- Improved network compatibility and throughput
- A more streamlined first-time setup and onboarding experience
- Enhanced enterprise management with stronger policy control, security, and governance
Networking improvements are particularly significant, addressing past issues with mirrored networking that caused “No route to host” errors. Additionally, a new dxgkrnl driver patch has been submitted to improve GPU support for WSL2, introducing compute-only GPU capabilities and support for multiple virtual GPUs.
Pavan Davuluri, Microsoft VP for Windows and Devices, emphasized ongoing quality improvements for Windows 11, including reducing Copilot integration in built-in applications, enhancing Bluetooth and USB reliability, and improving search functionality and responsiveness. Despite these commitments, concerns remain, such as the mandatory Microsoft Account sign-in requirement.