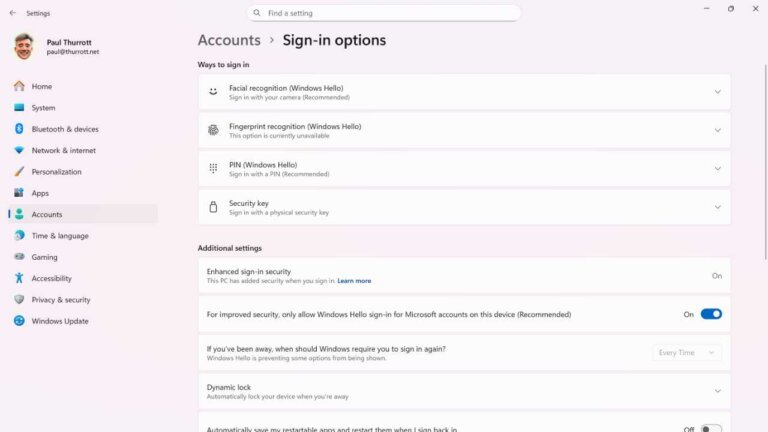
In Android devices, users can manage app permissions through a privacy dashboard located in Settings > Security & Privacy > Privacy > Permission manager. This includes permissions for the camera, microphone, location, and more. Users can specify access levels for these features, including allowing access all the time, only while using the app, or not at all. Special permissions, which allow apps to modify system settings or access sensitive data, require particular attention and can be reviewed in Settings > Apps > Special app access. Caution is advised for apps from outside the Google Play Store, as they may pose greater risks. Regular audits of app permissions are recommended to ensure that apps do not have more access than necessary.