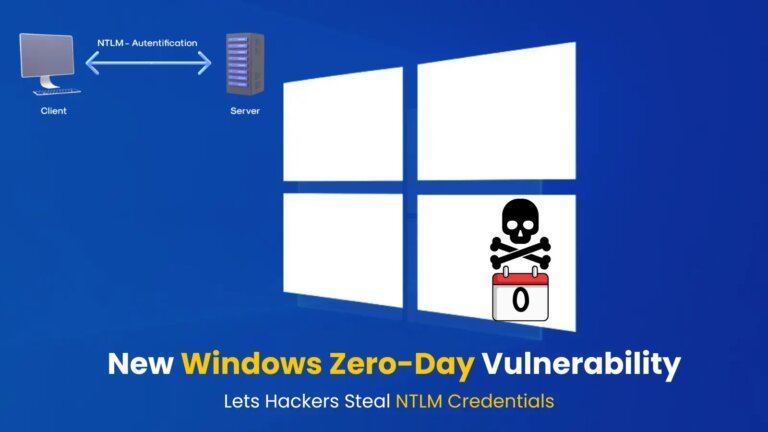
In early 2023, Microsoft announced the end of official support for Windows 10 by 2025, with regular updates and security patches ceasing on October 14, 2025. Users have options such as upgrading to Windows 11, switching to Linux, or subscribing to Microsoft's Extended Security Updates (ESU), which will end in October 2026. 0patch is a third-party service that provides micropatches for Windows 10, addressing specific vulnerabilities identified by security researchers. The service offers a free tier for zero-day patches and a paid Pro plan that includes legacy patches and post-End of Service updates. The free version should be used alongside Microsoft's ESU for comprehensive protection. 0patch plans to support Windows 10 until at least October 2030. The Pro plan is priced at approximately €35 annually, with a 30-day trial available. Users have reported some performance issues after installing patches, but the updates are lightweight and do not significantly affect system performance. Uninstallation is straightforward, and users can opt out at any time.