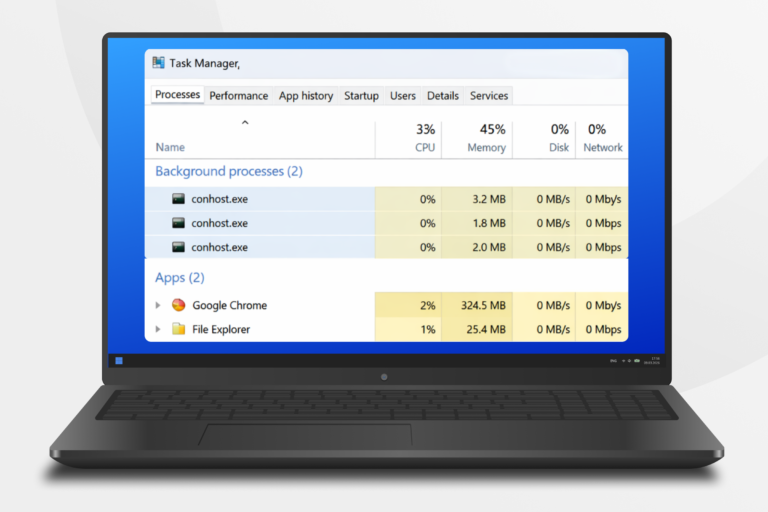
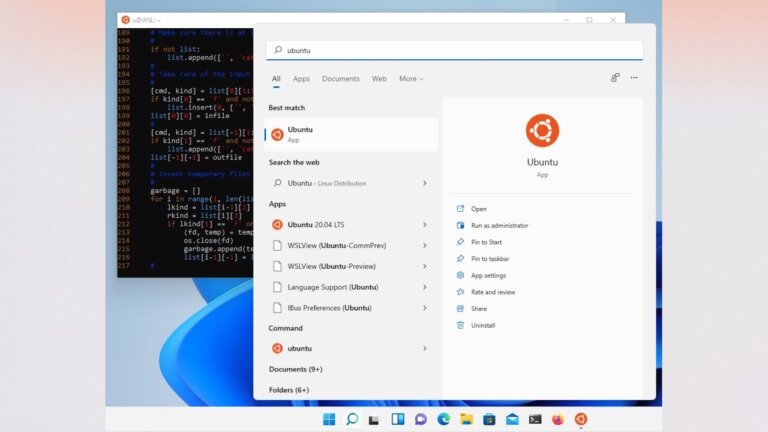
France has announced its intention to transition some of its government systems from Windows to Linux to reduce reliance on American technology. The initial phase will involve machines used by the Interministerial Directorate for Digital Affairs (DINUM), although a timeline for the transition has not been established. French Minister David Amiel stated that this move is part of a broader effort to regain control of digital sovereignty. Earlier this year, France banned public officials from using American videoconferencing platforms such as Google Meet, Zoom, and Teams. The European Commission is drafting legislation to promote tech sovereignty, but there are concerns about the security implications of moving away from American technology. Transitioning to Linux will require French government employees to adapt to open-source software, potentially replacing Microsoft Office 365 with alternatives like LibreOffice.