Windows 11 update KB5083631 introduces enhancements for user experience on PCs, available for download via Windows Update or direct links. The update is identified as “2026-04 Preview Update (KB5083631) (26200.8328)” and updates the OS to Build 26200.8328 for version 25H2 or Build 26100.8328 for version 24H2.
Direct download links for Windows 11 KB5083631 include:
- Build 26200.8328, 4802.0 MB, Windows 11 25H2, x64-based
- Build 26200.8328, 4802.0 MB, Windows 11 25H2, arm64-based
- Build 26100.8328, 4449.0 MB, Windows 11 24H2, x64-based
- Build 26100.8328, 4449.0 MB, Windows 11 24H2, arm64-based
Key features of the update include:
1. Introduction of Xbox Game Mode to standard PCs, allowing users to access a gaming-centric interface with an Xbox dashboard. The feature is gradually rolling out, and users can enable it manually using ‘ViveTool’.
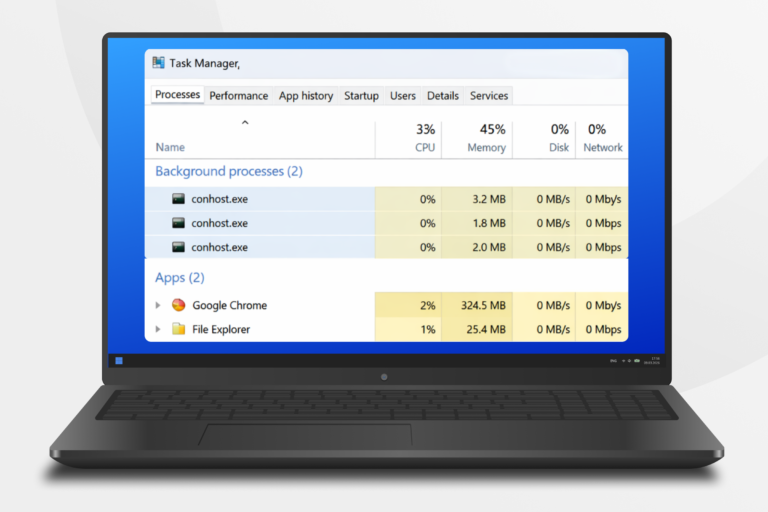
2. Improvements to File Explorer, including faster performance and consistent folder views, ensuring a reliable experience regardless of access method.
Users can download this optional update without major issues reported.