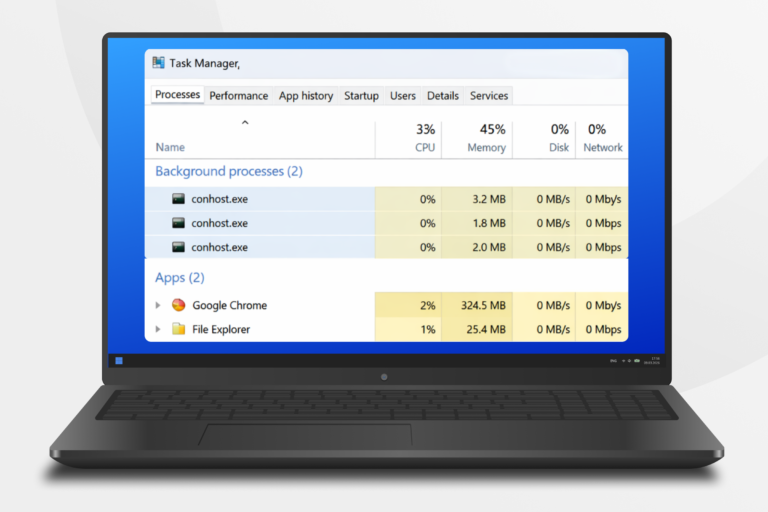
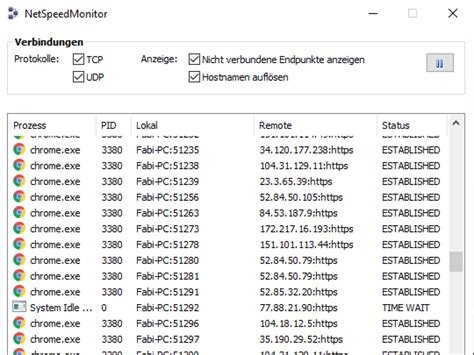
Recent reports indicate that the hardware monitoring tools HWMonitor and CPU-Z have been compromised, leading to users downloading malware instead of the legitimate software. Users reported receiving suspicious executable files and antivirus alerts when attempting to download the latest versions. A specific incident involved a user who downloaded HWMonitor from the official CPUID website, only to find the file was labeled incorrectly and flagged as a virus by Windows Defender. Cybersecurity experts confirmed that this is a serious issue involving a multi-stage trojanized attack from a compromised domain. The developer of CPU-Z and HWMonitor acknowledged that a secondary feature linked to the website was compromised for about six hours, causing the main website to display incorrect files. Users are advised to refrain from downloading or updating these utilities until the issue is resolved.