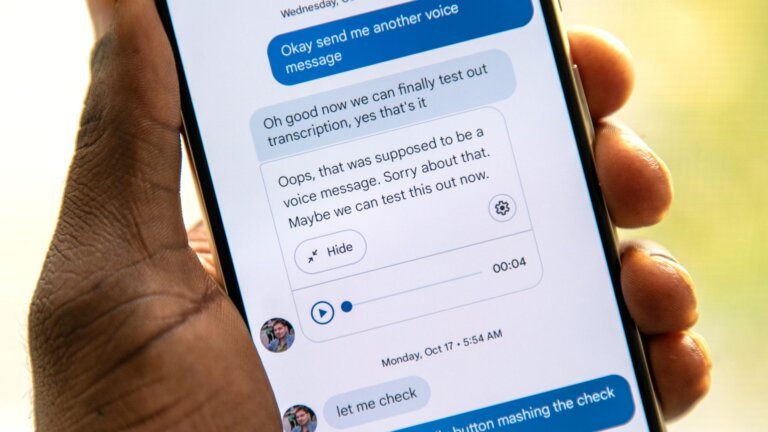
Samsung will officially cease operations of its Samsung Messages app in July 2026 and has stopped pre-installing it on newer Galaxy devices, including the Galaxy S26 series. Users can continue to send messages through the app until the shutdown, but emergency services and specific contacts will not be supported. Samsung is directing users to Google Messages as the official alternative, which supports Rich Communication Services (RCS) and is the default messaging app on most Android devices. Google Messages offers features such as reliable cross-texting with iPhone users, typing indicators, high-quality media sharing, message reactions, and built-in spam protection. Alternatives to RCS include WhatsApp, which offers voice and video calls, group chats, and message reactions, but has raised privacy concerns. Telegram allows large group chats, channels, and file sharing but lacks end-to-end encryption by default. Signal provides end-to-end encryption for all communications and collects minimal user data, making it the most secure option. Customizable SMS apps like Textra and QUIK SMS do not support RCS, making Google Messages the most viable option for RCS functionality.