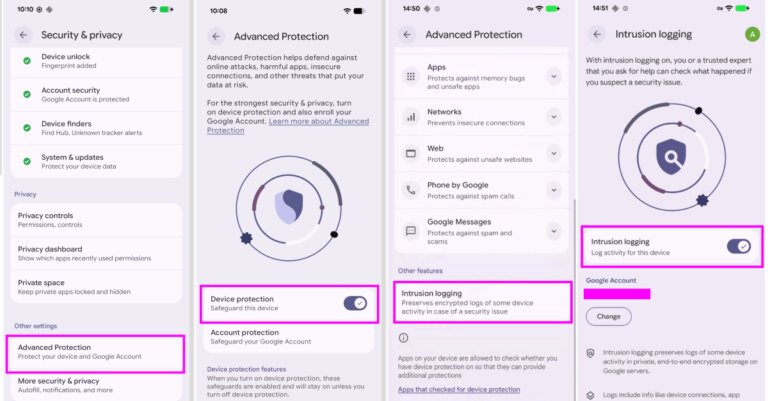
Most individuals do not require antivirus apps on their smartphones, as the primary threats have shifted from traditional viruses to scams and deceptive practices. iPhones utilize app isolation, making them less susceptible to conventional viruses but vulnerable to scams like phishing and fraudulent messages. Android phones allow sideloading, increasing the risk of malware from unofficial sources. The main threats include phishing texts, fake login pages, scam calls, reused passwords, and social engineering tactics. To enhance security, users should keep their phones updated, use strong passwords, enable two-factor authentication, avoid suspicious links, and refrain from installing apps from unknown sources. Antivirus apps may be helpful in specific situations, such as frequent link tapping or downloading files from unfamiliar websites, with reputable companies offering mobile security solutions focused on scam detection and account safety.