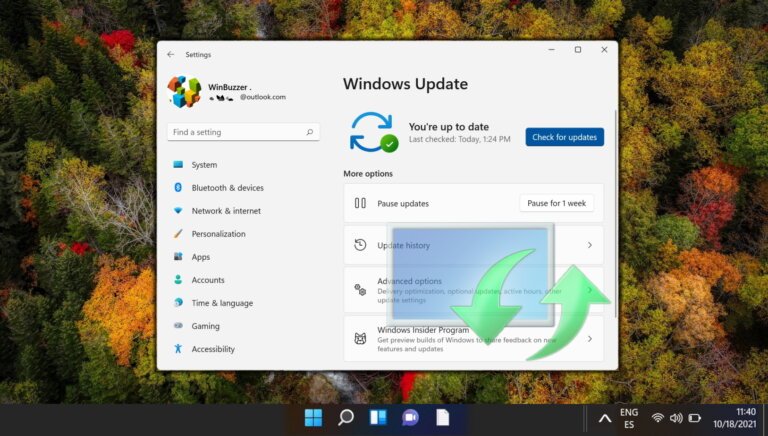
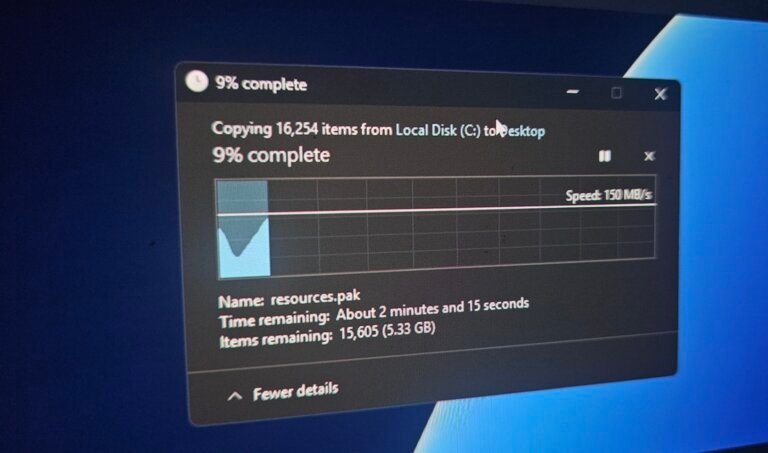
On March 31, Microsoft released emergency update KB5086672 in response to issues caused by the previous preview patch KB5079391, which left many Windows 11 devices in a loop with error code 0x80073712, blocking access to March security fixes. Microsoft withdrew KB5079391, which was launched on March 26, and replaced it with KB5086672, a cumulative update that includes all fixes from March 2026. KB5086672 supersedes previous updates, including KB5079473, KB5085516, and KB5079391. Users with the "Get the latest updates as soon as they’re available" setting will receive KB5086672 automatically, while others can manually check for updates or download it from the Microsoft Update Catalog. Microsoft has been issuing multiple emergency updates recently, raising concerns about the quality of its update pipeline, with a history of emergency patches for various issues affecting Windows 10, Windows 11, and Windows Server. The issues from KB5079391 may resurface in the upcoming April cumulative update.