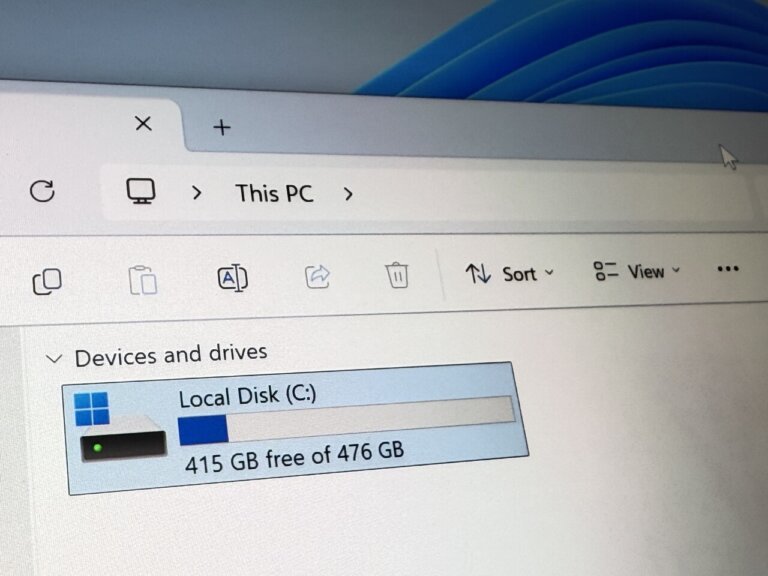
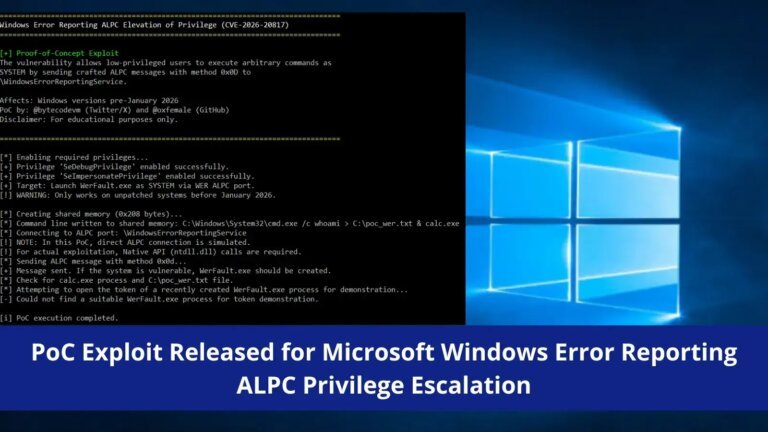
The March 2026 Windows 11 update (KB5079473) has caused significant issues for users, including inaccessible C: drives, system crashes, and freezing. Reports indicate that Samsung Galaxy Book device owners are particularly affected, with complete blockage of access to the C: drive. Microsoft acknowledges the "C: is not accessible - Access denied" issue, linking it to the Samsung Galaxy Connect application, and is working on a resolution. The affected devices include various models of the Samsung Galaxy Book 4 and certain Samsung Desktop models running Windows 11 versions 24H2 and 25H2. While Microsoft claims only Samsung users are impacted, it is unclear if other manufacturers are experiencing similar problems. The update has raised concerns about the quality assurance processes prior to releases.