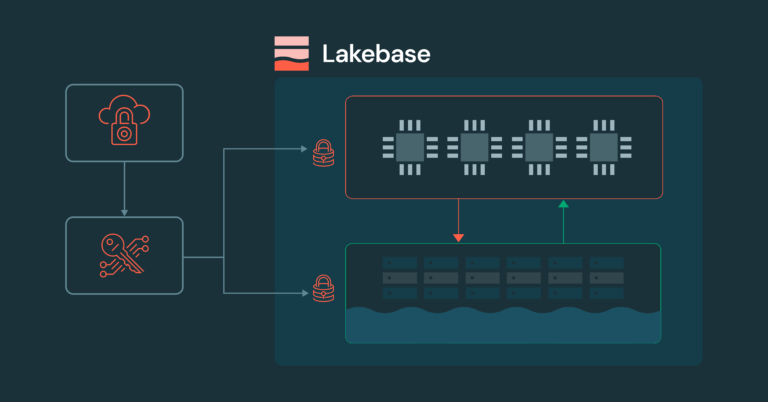
Encryption at rest is essential for cloud environments, especially in regulated sectors. Lakebase offers Customer Managed Keys (CMK), allowing organizations to control their encryption keys from preferred Key Management Services (KMS) like AWS KMS, Azure Key Vault, or Google Cloud KMS. Lakebase CMK manages both persistent storage and ephemeral compute, ensuring data security.
Lakebase's architecture separates storage and compute layers, enabling elastic scaling and serverless operations. The storage layer maintains persistent data, while the compute layer consists of dynamic Postgres instances. This separation poses encryption challenges, addressed by Lakebase CMK through a hierarchical Envelope Encryption model.
The key hierarchy includes:
1. Customer Managed Key (CMK): The Root of Trust in the cloud KMS, never accessed in plaintext by Databricks.
2. Key Encryption Key (KEK): A transient key for wrapping data keys.
3. Data Encryption Keys (DEKs): Unique keys for each data segment, stored in an encrypted state.
When data access is needed, Lakebase retrieves DEKs by unwrapping keys from the KMS. If a key is revoked, access to the data is denied, and ephemeral compute instances are terminated.
In practice, CMK applies to:
1. Persistence Layer (Storage): All data segments are encrypted with keys controlled by the CMK.
2. Ephemeral Layer (Compute): Each compute instance generates a unique ephemeral key, and upon revocation, the instance is terminated, destroying in-memory keys.
CMK implementation follows a delegation model, allowing Security Admins to manage keys without accessing data. The process includes key configuration, workspace binding, and lifecycle management. Key rotation is seamless, requiring no data re-encryption.
All cryptographic operations involving the CMK are logged by the cloud provider's audit service. Lakebase CMK is available for Enterprise tier customers, allowing organizations to manage their encryption keys effectively.