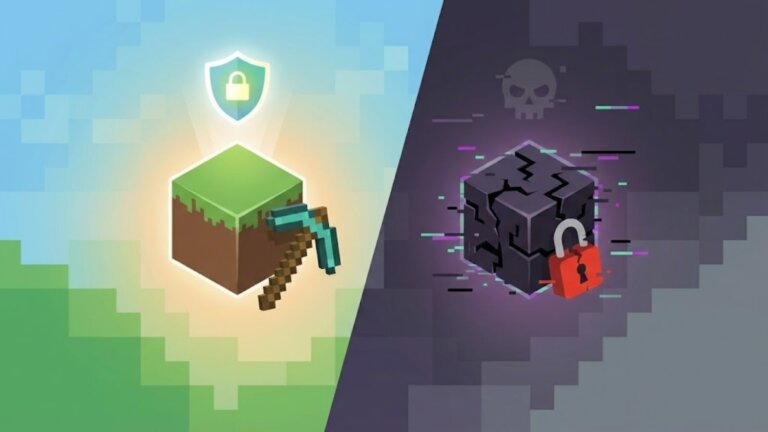
Google is implementing a new flow for installing applications from unverified developers on Android, which includes several steps to reduce risks associated with sideloading. Users must first enable developer mode, followed by a verification check to ensure no external influence is guiding the installation. They then restart their devices and reauthenticate, disrupting any potential remote access. A one-day waiting period is enforced before installation, allowing users time to reconsider. Finally, users must confirm their action using biometric authentication or a device PIN. After successful verification, users can install apps from unverified developers for a limited duration or indefinitely, with warnings about the app's source provided throughout the process.