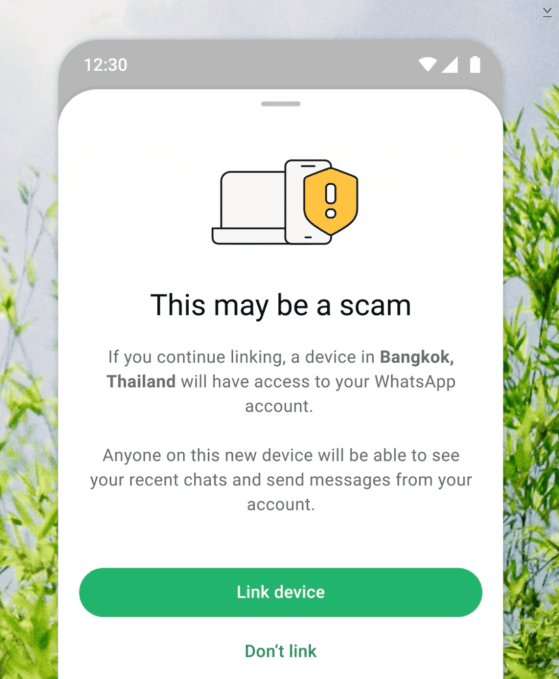
The United States has issued a warning about cyber actors linked to Russian intelligence targeting users of commercial messaging applications, particularly Signal, compromising thousands of accounts worldwide. The FBI and CISA released a public service announcement detailing the operation's focus on individuals of “high intelligence value,” including U.S. government officials, military personnel, political figures, and journalists. Attackers have not breached the encryption of these platforms but manipulate users into disclosing credentials or linking devices. Russian intelligence-linked actors often pose as official support accounts, creating urgency to obtain security codes. Dutch intelligence agencies also reported a similar campaign targeting Signal and WhatsApp accounts of dignitaries and military personnel. Users are urged to be cautious of suspicious messages and to avoid sharing personal information. Signal reaffirmed that its encryption remains intact, emphasizing that vulnerabilities arise from user behavior rather than technical flaws in the application itself.