Concerns about online safety have led to increased use of Android spy apps, which provide access to messages, calls, and real-time locations. Testing shows that top apps can sync data in under 5 seconds and track over 15 social platforms. Users can monitor behaviors and interactions through a single dashboard, with effective tools operating in stealth mode.
uMobix is highlighted as the best Android spy app, scoring 9.8/10, with real-time updates every 3–5 seconds, access to calls, SMS, deleted messages, and GPS locations. It supports tracking for over 30 data types and has a starting price of .99/month.
XNSPY, scoring 9.5/10, offers detailed monitoring with call and SMS updates every 10–15 seconds and remote control features, starting at .99/month.
xMobi, rated 9.2/10, provides essential features with quick setup and a responsive dashboard, starting at .99/month.
SpyBubble Pro, scoring 9.0/10, specializes in stealth monitoring with data syncing every 15 seconds, starting at .49/month.
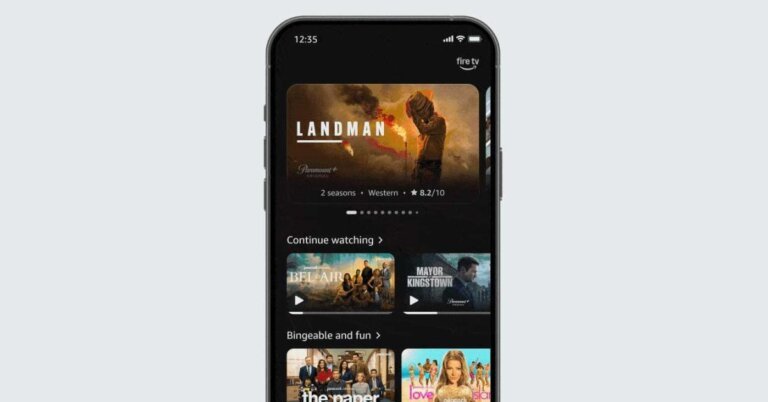
AccountViewer, rated 8.9/10, focuses on social media insights, starting at .99/month.
PeekViewer, scoring 9.1/10, allows anonymous profile viewing, starting at .99/month.
mSpy, rated 9.4/10, is designed for parental control, starting at .99/month.
Effective Android spy apps should provide real-time tracking under 10 seconds, support multiple social platforms, and operate in stealth mode. Installation typically requires physical access to the device, and monitoring begins immediately after setup. The legality of using these apps depends on consent and local laws.