Cyber threats have evolved significantly in the past five years, introducing AI-driven phishing attacks, fileless malware, and rapid ransomware attacks. Traditional antivirus software is struggling against these advanced threats. Effective strategies for computer security in 2025 include reinforcing systems, implementing robust network defenses, and selecting appropriate security tools.
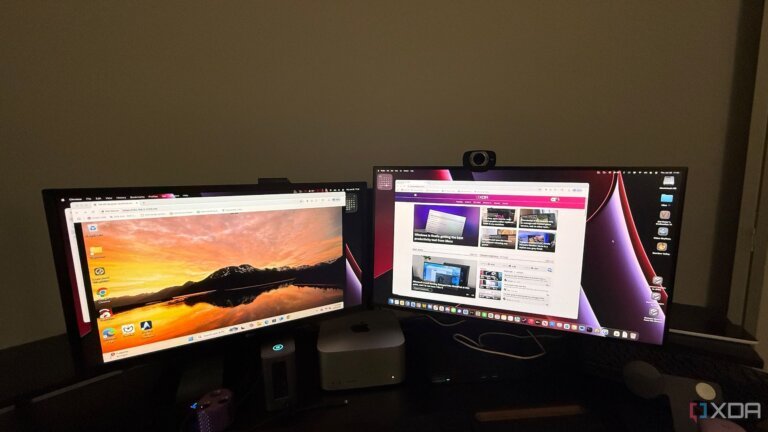
NinjaOne and AnyDesk are highlighted as leading security solutions. NinjaOne focuses on endpoint management and monitoring, featuring built-in BitDefender antivirus and real-time monitoring, while AnyDesk provides secure remote desktop access with military-grade encryption and session recording.
Computer virus prevention involves addressing vulnerabilities in system configuration, network defenses, user habits, and outdated software. Key practices include disabling unnecessary services, configuring firewalls, educating users about phishing, and ensuring timely software updates.
NinjaOne offers proactive malware protection through behavioral monitoring, automated updates, and instant remote intervention. Pricing starts as low as [openai_gpt model="gpt-4o-mini" prompt="Summarize the content and extract only the fact described in the text bellow. The summary shall NOT include a title, introduction and conclusion. Text: You are now confronted with cyber threats that were virtually unheard of just five years ago. The landscape has evolved dramatically, introducing AI-driven phishing attacks, fileless malware that exists solely in memory, and ransomware capable of encrypting entire networks in mere moments. This raises an important question: how effective are your five-year-old security measures in this new environment?
Traditional antivirus software, once a staple of computer security, now struggles against these advanced cyber threats. Fortunately, there are effective strategies to bolster your defenses and safeguard your systems.
Today, we’ll explore how to prevent viruses and malicious code using strategies that are relevant for 2025. You will learn how to reinforce your systems, implement robust network defenses, and select computer security tools that can intercept threats before they can execute.
Quick Snapshot: Top Computer Security Solutions for 2025
Among the leading solutions, both NinjaOne and AnyDesk play pivotal roles in enhancing your computer security defenses, albeit in different ways. Here’s a comparative look:
NinjaOne
AnyDesk
Primary Function
Endpoint management & monitoring
Secure remote desktop access
Best For
IT teams managing multiple devices
Remote support & work-from-home security
Malware Protection
Built-in BitDefender antivirus, behavioral detection
Prevents malware transmission during remote sessions
Key Security Features
Real-time monitoring, automated patching, USB blocking
Military-grade encryption, whitelist access, session recording
Starting Price
Custom pricing (as low as .50/month for 10,000 endpoints)
Free for personal use, €22.90/month for business
Free Trial
14 days with full features
Free version available, paid plans billed annually
Understanding Computer Virus Prevention & System Hardening
Computer virus prevention begins with recognizing that malware exploits vulnerabilities in four critical areas: system configuration, network defenses, user habits, and outdated software. System hardening involves proactively closing these security gaps before they can be exploited.
Start by disabling unnecessary services and ports. Each running service represents a potential entry point for malware. Turn off file sharing when it’s not needed, disable remote desktop access unless actively in use, and restrict administrator rights from daily user accounts.
Next, focus on your network. Configure your firewall to block all incoming connections except those you specifically allow. Employ DNS filtering to prevent access to known malicious sites. Segment your network to contain breaches and enable WPA3 encryption on your Wi-Fi, while also changing default passwords on all network devices.
After adjusting device settings, it’s time to modify risky user habits. Educate yourself and your team to recognize phishing attempts. Avoid opening unexpected attachments, even from known contacts, as their accounts may have been compromised. Always verify suspicious requests through a different communication channel.
Lastly, ensure that you update your software. Regular updates patch security vulnerabilities that could be exploited by spyware and other threats. Enable automatic updates for your operating system and browsers, and update all software within 48 hours of patch releases, as attackers often target unpatched systems immediately after vulnerabilities become public.
NinjaOne: Enterprise-Grade Malware Protection
NinjaOne adopts a proactive stance on malware protection, shifting the focus from reactive measures to continuous monitoring of your IT infrastructure. Unlike traditional methods that rely on signature-based detection, NinjaOne employs behavioral monitoring to identify unusual activity patterns indicative of a compromise.
Main features of NinjaOne
Real-time antivirus protection: Integrated antivirus software powered by BitDefender scans continuously without hindering system performance.
Automated software updates: Critical security updates are executed automatically, thwarting attackers before they can exploit vulnerabilities.
Comprehensive dashboard: Monitor every device in real-time from a single interface, including running processes and active network connections, while detecting file encryption that signals ransomware attacks.
Instant remote intervention: Quickly connect to infected machines to terminate malicious processes and restore normal operations within minutes.
Automated security enforcement: Implement computer security standards across all devices, block USB ports to prevent spyware introduction, restrict unauthorized software execution, and quarantine suspicious devices.
NinjaOne pricing
NinjaOne offers custom pricing tailored to your needs, starting as low as .50 per month for 10,000 endpoints, with rates increasing up to .75 for 50 or fewer endpoints. Pricing may vary based on region and specific requirements.
The platform also provides a 14-day free trial with full access to all features, allowing you to evaluate NinjaOne firsthand. Demos are available, but a money-back guarantee is not offered.
AnyDesk: Secure Remote Access Without Compromising Security
AnyDesk excels in providing secure remote desktop access without introducing new vulnerabilities to your computer security defenses. Utilizing military-grade encryption and stringent authentication protocols, AnyDesk ensures that remote sessions remain secure.
Best features of AnyDesk
TLS 1.2 encryption: All remote connections employ bank-level encryption, preventing unauthorized intervention and data modification during transmission.
Whitelist-only access: Configure AnyDesk to accept connections only from pre-approved device IDs, effectively blocking unauthorized access attempts. Specific access levels can also be granted for each session, minimizing potential damage from compromised accounts.
Session recording: AnyDesk’s built-in screen recording tool enables documentation of all remote activities for security audits and compliance, aiding in the detection of suspicious behavior patterns.
No cloud relay option: Direct peer-to-peer connections eliminate reliance on cloud servers, reducing the attack surface for sensitive operations.
AnyDesk Pricing
AnyDesk offers a tiered pricing structure, including a free option. The free tier is limited to one device and includes basic features, making it ideal for personal use or initial testing.
The first paid tier starts at .90 per month, covering one licensed user and one outgoing session, with support for up to 100 unattended devices. Pricing can reach as high as .90 per month for 100 users and 1,000 unattended devices, along with additional features such as CLI, mass deployment (MSI), and phone support. For more extensive needs, custom subscriptions can be arranged through customer support.
Choosing the Right Anti-Virus Software
Modern antivirus solutions must encompass capabilities that were not available when Norton Antivirus first debuted in 1991. Today’s threats are adept at hiding in memory, encrypting files for ransom, and pilfering credentials without triggering conventional virus scans.
Effective virus protection now requires a combination of multiple detection methods: signature matching for known threats, behavioral analysis for zero-day attacks, and cloud intelligence that shares threat data globally in real-time.
To ensure comprehensive protection, seek antivirus software that includes web protection to block malicious sites before they load, email scanning to catch phishing attempts and infected attachments, and ransomware protection that monitors file changes to thwart encryption attacks.
A robust computer security software package should also feature a firewall, password manager, and VPN. Performance impact is a critical consideration; some products can significantly slow down your system, while others operate seamlessly in the background.
What are the most dangerous types of viruses in 2025?
The most destructive types of malware in 2025 extend far beyond traditional computer viruses that merely replicate themselves. Today’s threats are engineered to steal money, dismantle businesses, and compromise national infrastructure.
Ransomware: This is arguably the most financially devastating threat. Ransomware attacks steal data, encrypt files, and threaten to publish sensitive information unless a ransom is paid. Recovery costs average million per incident, according to IBM's 2024 security report, excluding downtime and reputational damage.
Fileless malware: This type of malware resides in your computer's memory, leaving no trace and evading traditional antivirus scans that search for malicious files.
Info-stealers: These stealthy programs monitor your activities and harvest sensitive information, such as passwords and cryptocurrency wallet details, while remaining undetected.
AI-powered malware: The latest threat category employs machine learning to evade detection, tailor attacks for specific targets, and autonomously generate new malicious code. They adapt their tactics in real-time, making them exceptionally challenging to combat with conventional protection methods." max_tokens="3500" temperature="0.3" top_p="1.0" best_of="1" presence_penalty="0.1" frequency_penalty="frequency_penalty"].50 per month for 10,000 endpoints, with a 14-day free trial available.
AnyDesk uses TLS 1.2 encryption for secure remote connections and allows whitelist-only access. Its pricing includes a free tier for personal use and starts at .90 per month for business use.
Modern antivirus solutions must combine signature matching, behavioral analysis, and cloud intelligence to combat sophisticated threats. Effective antivirus software should also include web protection, email scanning, and ransomware protection.
The most dangerous types of malware in 2025 include ransomware, fileless malware, info-stealers, and AI-powered malware, which are designed to steal money, dismantle businesses, and compromise infrastructure. Ransomware recovery costs average over million per incident, excluding downtime and reputational damage.