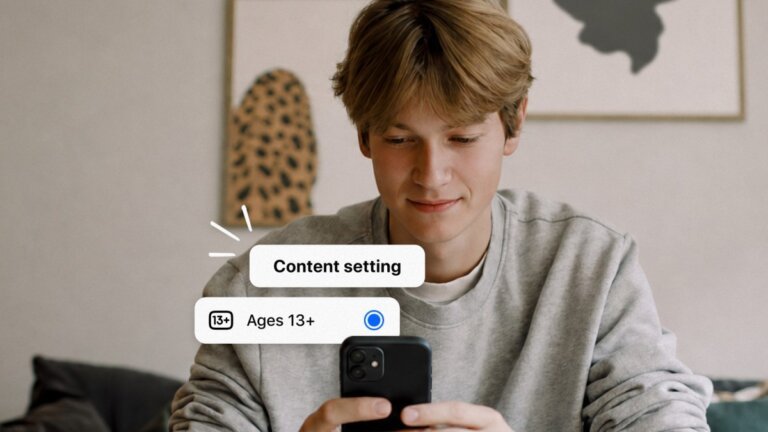
Meta is enhancing protections for younger users by expanding its Teen Accounts framework across Facebook, Messenger, and Instagram. This includes implementing stricter content settings that limit exposure to inappropriate material, such as violence and self-harm. A new "Limited Content" setting will be introduced for Facebook and Messenger to provide additional content restrictions. Additionally, Instagram is testing a feature to diversify content recommendations for teens, reducing repetitive exposure to similar topics. These initiatives come amid increased regulatory scrutiny regarding youth safety on social media platforms.